Social Engineering in Crypto Scams
Pig-butchering, fake support, and confidence tricks steal more crypto than protocol breaks — how social engineering works and how users can resist.
The stereotypical image of a hacker stealing cryptocurrency straight out of Hollywood: a dark hooded figure in front of the keyboard, breaking through peripheral firewalls and hacking into sophisticated encryption algorithms with handcrafted code. It is a purely technical view of what cybercrime looks like. The truth is often far more prosaic – and frankly, human.
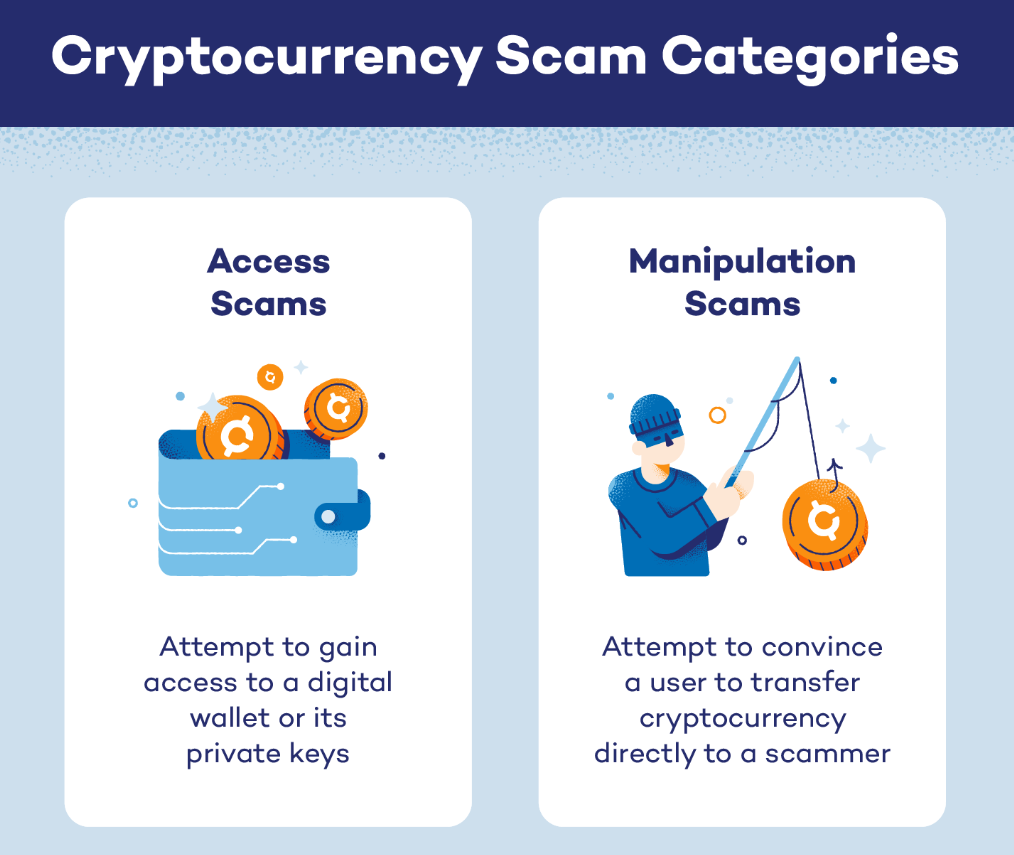
There are technical attacks one can execute, sure, but far more crypto is stolen not by breaking the blockchain but by breaking the user. This is the province of social engineering — the practice of manipulating people into divulging confidential information or taking actions that are not in their best interest. It’s not about zero-day hacks, but good old parlor tricks, confidence games, and knowing the blind spots of human psychology.
In the wild west of digital assets — where transactions are irreversible and people can operate outside the reach of police or courts should they want to, anonymity is at a premium — humans are the weakest link. Scammers know the work involved in hacking a decentralized network is much more difficult than hacking into a person’s trust, fear or greed. Either way, by getting through the door simply by asking the user to open up, these bad actors have bypassed even the most secure security controls due to employing human behavior and not technology.
In this piece, we’ll dissect the most common social engineering methods currently affecting the crypto community, concentrate on the psychological bases they exploit, and propose ways to protect against them.
Long Con and Trust Trap
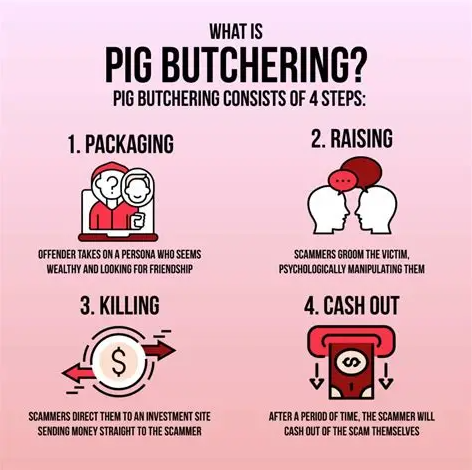
“Sha zhu pan,” or “pig butchering” in Mandarin, is one of the many new forms of social engineering that netizens in China use to describe the schemes they encounter. This metaphor paints a clear picture of the process: the victim is the “pig” that’s been “fattened up” with flattery, friendship and faux investment returns before being “slaughtered” for everything they’re worth. Unlike smash-and-grab phishing operations, this is a long game that depends on exploiting the psychological urge for connection and gradual attrition of skepticism.
It is often innocuous in the early stages — a wrong number text, a direct message on social media or even an encounter through friends. The scammer doesn’t go right into crypto. Instead, they seek to establish a relationship. They could pretend to be an entrepreneur with a successful career, or a professional who is lonely or traveling.
Over weeks or months, they develop a real relationship with the victim. They swap photos of the meals they are eating, chat about their hobbies and empathize with the victim’s long-lost personal struggles. This phase is meant to bring down the defenses of the victim. There is a biological mandate to trust those we come into contact with frequently, particularly if that person seems genuinely interested in our lives.
After they have won a degree of confidence, scam artists will typically bring up money – but not anything direct. They may casually reference a “big win” they had in the market or post a screenshot of an extravagant purchase made with trading profits. The trap is made when the victim sounds interested. And instead of being a salesman, the scammer is a mentor who doesn’t really want to help: “I’ll kind of show you what I did and that side kind of worked.” They instruct the victim to deposit money in a bogus trading platform that appears real, often emulating the interface of popular exchanges.
To make the con convincing and to create a “small win,” the scammer will sometimes also contrive this. They urge the sucker to stake a modest sum of money, then to withdraw their first profit. This is the psychological hook. The victim’s brain gets flooded with dopamine; the doubts vanish, replaced by a rush brought on by the possibility of free money and appreciation for their new friend. The victim believes the con is legitimate, and they end up putting their life savings into it with complete confidence. Only when they attempt to withdraw the enormous sum do they come face to face with reality: that they’ve been catfished, and the money only exists as numbers on a computer screen, just like their defunct friend.
Counterplay: To avoid being manipulated by such a deep emotional connection, you must be strict with yourself and keep your social life completely separate from financial choices. The golden rule is a simple one: strangers on the internet don’t want to make you rich. If you have a new online friend or romantic interest who is talking about investing, raise the red flags immediately. Do a reverse image search of any photos they send; scammers frequently use stolen pictures of beautiful models or popular influencers. Push for a video chat early in the courtship. Being asked to bring money to a platform that, if it is able to exist, can thrive only on speculation should give you pause. Just don’t move any money — at all — anywhere without meeting face-to-face with someone who says they have the power to make you rich. If you are in doubt, go ahead and attempt to withdraw your money. If there’s an excuse, or a “tax” needed to withdraw, stop all communication — it’s a scam.
Authority Trap and Urgency of Crisis
Another potent switch is the public’s natural inclination to obey authority, and the tendency of human beings to panic amid a crisis. Using this, scammers impersonate the support team of exchanges, wallet providers or even governmental departments. The strategy depends upon creating a mentally chaotic state of high anxiety in which one’s thinking goes limp.
Let’s say you are attempting to send USDT to a friend and for some reason the transaction seems to be blocked. You look for a support number or tweet about the problem. Almost instantly, a “helpful” account responds or you stumble upon a phone number that appears to be official. The voice at the other end is professional, calm, authoritative. They say your money is “stuck” or your account is “compromised” and you must act fast to save what you have.
And this urgency is not real, it’s there to pressure you into doing something without even thinking about it. The “support agent” may instruct you to download remote desktop software so he can “fix” the problem or to hand over your seed phrase so he can “verify” that you own the wallet. You’re also afraid of losing your money, and this person sounds intelligent, so you follow instructions. No real support agent would ever request your seed phrase, or require remote access to your computer.
There is now a terrifying new layer to this tool, Deepfake technology. Now con artists can apparently use AI to replicate the voices of CEOs, or other distantly placed executives they trust, leaving voicemails and even placing live calls indistinguishable from those made with the CEO’s normal devices. This is authority bias taken to the next level. If you hear a well known figure telling you to send money to an address that is for a “giveaway” or an “emergency upgrade,” your brain is just wired to believe them.
Counterplay: The only effective antidote to attacks based on authority is a “zero-trust” posture toward incoming communication. If someone calls you claiming to be from your bank or crypto exchange, do not answer; hang up. If you get an email saying your account is locked, do not click the link. Instead, go to the official website via your own bookmarks – not by clicking a link on a search engine or in a message – and contact support through their real channel. Don’t forget that real organizations don't function in real time and never require you to stay on the line, or rush your response, within seconds otherwise you will lose your money. With respect to seed phrases, think of them like you would a combination to a physical vault: there is no situation, technical or otherwise where an agent should need that combination in order to come help you. Ask them and they are taking you for a chump.
Unseen Signature and Approval Phishing
As the crypto space shifted to decentralized finance (DeFi), scammers have adjusted accordingly by taking advantage of the intricacy around how smart contracts interact. This approach, also known as “approval phishing” or “drainer” attacks specifically leverages the user’s technical ignorance when it comes to what they’re actually authorizing.
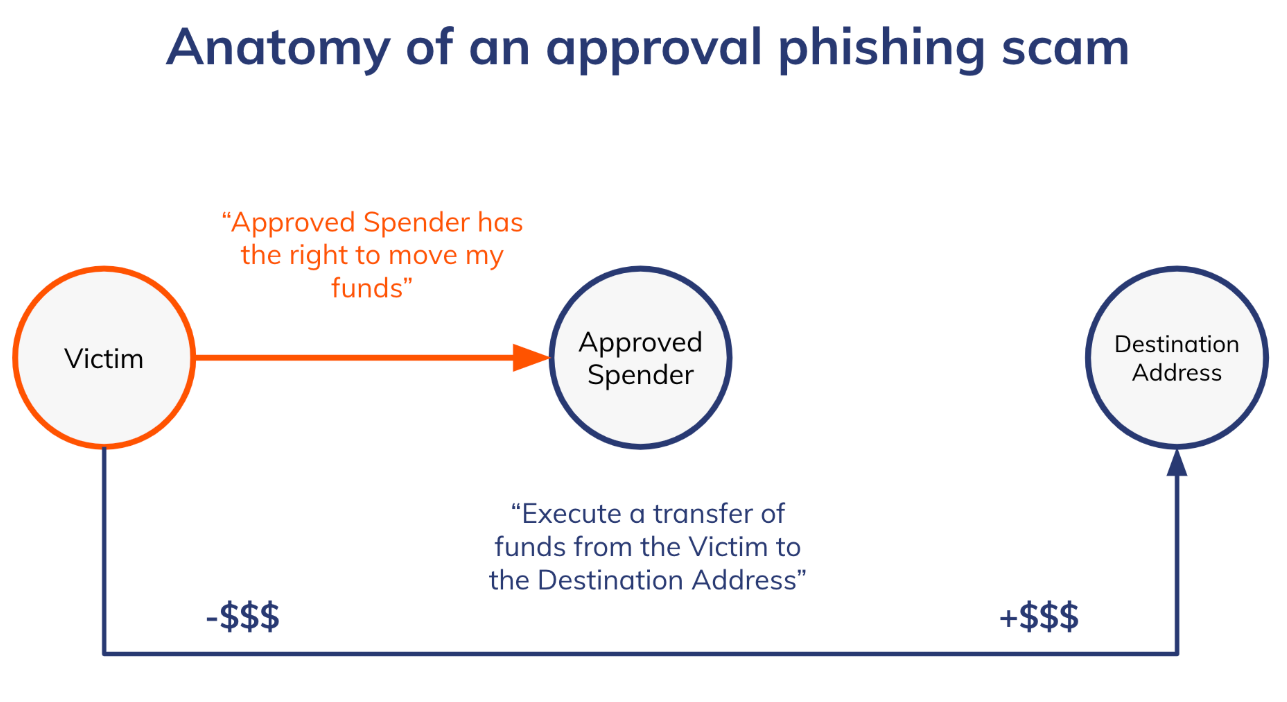
In this case, a user could end up on a site that is identical to a popular NFT marketplace or DeFi protocol. They could be enticed by a promise of a free “airdrop,” a term used in the industry for free tokens, or an exclusive “minting” opportunity. The site requests for the user to connect their wallet and sign a transaction when ready to claim the reward.
The pop-up inside the wallet is often a wall of technical gobbledygook. The vast majority of users, conditioned by years of unfathomable Terms of Service with a click-through “I Agree” attitude, are going to click the big “Confirm” button and get their reward. But they are not signing a plain old login message. It’s usually a "SetApprovalForAll" function or the "Permit" signature. In non-coder terms: This signature gives the scammer’s smart contract carte blanche to transfer all of a particular asset (such as USDT or NFTs) out of the user’s wallet, no further confirmation required.
The psychology here is both greed (the free airdrop) and “learned helplessness” around technical interfaces. They figure, since they still have their seed phrase, they can get their money back. What they do not understand is that a digital signature can be as harmful as passing the keys. The scammer doesn’t have to know the seed phrase, at least not if you’ve unwillingly signed a permission slip that lets him drain the vault.
Counterplay: The defense against such approval phishing is to make a different assumption about how wallets wield their permission. Never treat a wallet signature as similar to pressing on a "login" or "confirmation" button. It’s something like a notarized legal contract — on the blockchain. Before you confirm any transaction, always read the details. Search for "Approve," "SetApprovalForAll," or "Permit." If you are attempting to claim a free item and the transaction requests your permission to access your USDT or other tokens, deny it. One way to do this is to use a “burner” wallet — one that you only keep small amounts of money in, used just for new or suspicious sites. This forms a firewall — if you make an error and sign a malicious contract, the scammer can only take whatever dust was in your burner wallet, not your entire savings. Also rely on browser extensions that translate transaction data into human-readable warnings, telling you if a signature looks like a wallet drainer.
Pattern Match Glitch and Poisoning of Addresses
One of the more insidious hacks depends on the way the human brain processes information for speedy consumption. And when users copy and paste cryptocurrency addresses, they rarely scroll all the way through those random digits and letters to ensure that the address is correct. Instead, they usually look at the first four or five characters and the last four or five characters. Scammers understand this mental shortcut — and manipulate it through “address poisoning.”
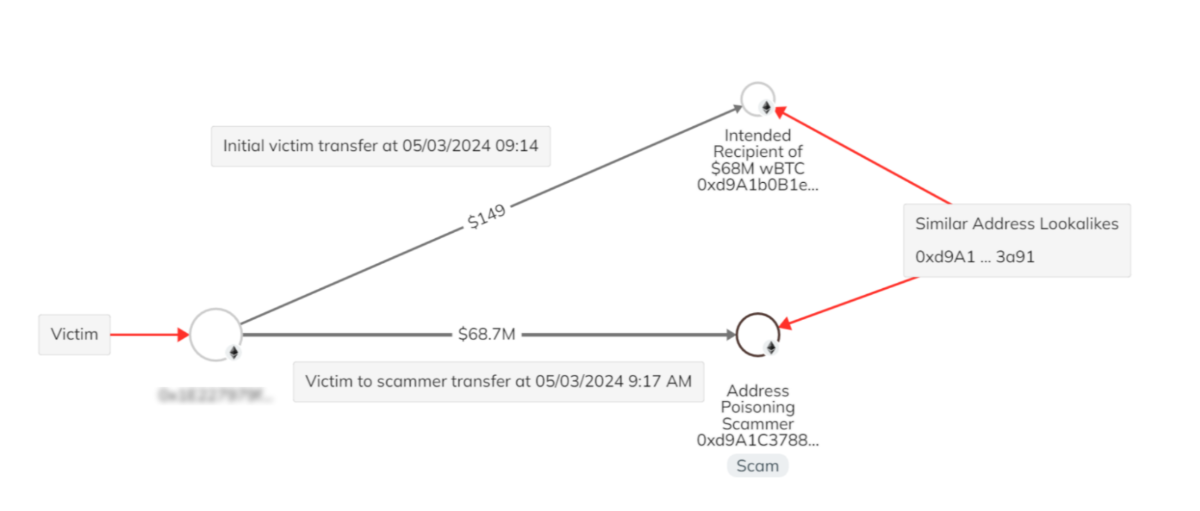
In this scam the fraudster watches the blockchain for people who are currently active. When they spot a user making a transfer — say, sending a great deal of USDT to their own personal cold wallet — the scammer employs software that can produce a “vanity address” that matches very closely with the intended destination. This fake address will have the identical first and last characters of the actual address, but be different in between.
After generating that lookalike address, the fraudster sends a transaction of 0 USDT (or close to that amount) from this counterfeit address to the victim’s wallet. This transaction is now reflected in the victim’s history. Then the next time the victim wishes to send USDT into their cold wallet, they may open the history and paste in the most recent address because that is likely what they last used. As long as the beginning and ending conform to what they remember, they don’t notice the departure. They start, pay the USDT fees as usual and deposit directly into the scammer’s wallet black hole.
This is taking advantage of “inattentional blindness” and the path of least resistance. The victim isn’t systemically “hacked” in the traditional sense; they are getting tricked into hacking themselves. The scammer’s theory of the case: No one will notice; we’re counting on laziness and the way autocomplete patterns.
Counterplay: The answer to address poisoning is validation. Never ever copy any address from your transaction history! It is a public ledger that anyone can write to — including scammers. You should never trust only the first or last few characters of an address when validating. Examine some random sequence in the middle of the string, or better every single character. The best way to do so is by using an address book function in your wallet. Whitelist your trusted addresses. You can also give addresses different names. That way you will be choosing a trusted place rather than a perhaps poisoned log.
Safe in a Zero-Trust World
What all these tactics have in common is that they subvert technical security by hacking the human OS. Whether that be the emotional tug of a romance scam, the fake time pressure tactics wielded by a help desk impersonator, the deliberately intricate maze of misdirection found in a scummy contract or imagery that deceives in an address poisoning attack, it's all about getting someone to act out and work against themselves.
Defense requires a mindset shift. In the traditional world of finance, banks serve as a safety net, alerting to and reversing unauthorized charges. In crypto, you are the bank. There is no fraud department to ring, and transactions can never be unwound. With this freedom, also comes the obligation of vigilance forever. Slow down. If the offer is too urgent, it’s probably a scam. When a stranger is incredibly helpful there is probably a catch. If a deal seems byzantine, it likely is.
By exposing these parlor tricks, you morph from an easy mark into a skeptical user. Blockchain is secure, it's the social layer that you have to always watch out for. Guard your mind the way you do your private keys.
On the subject of efficiency and being smart with your crypto you should not only know how to secure your transactions but also understand their mechanics. For TRON network active users Netts USDT Transfer Calculator is a must-have tool to save your $$$. All USDT transfers on TRON feature the consumption of certain network resources such as Energy and Bandwidth. In case a user’s wallet does not have any TRX, network will burn his/her last TRX to pay for the energy which normally costs 14-20 times higher.
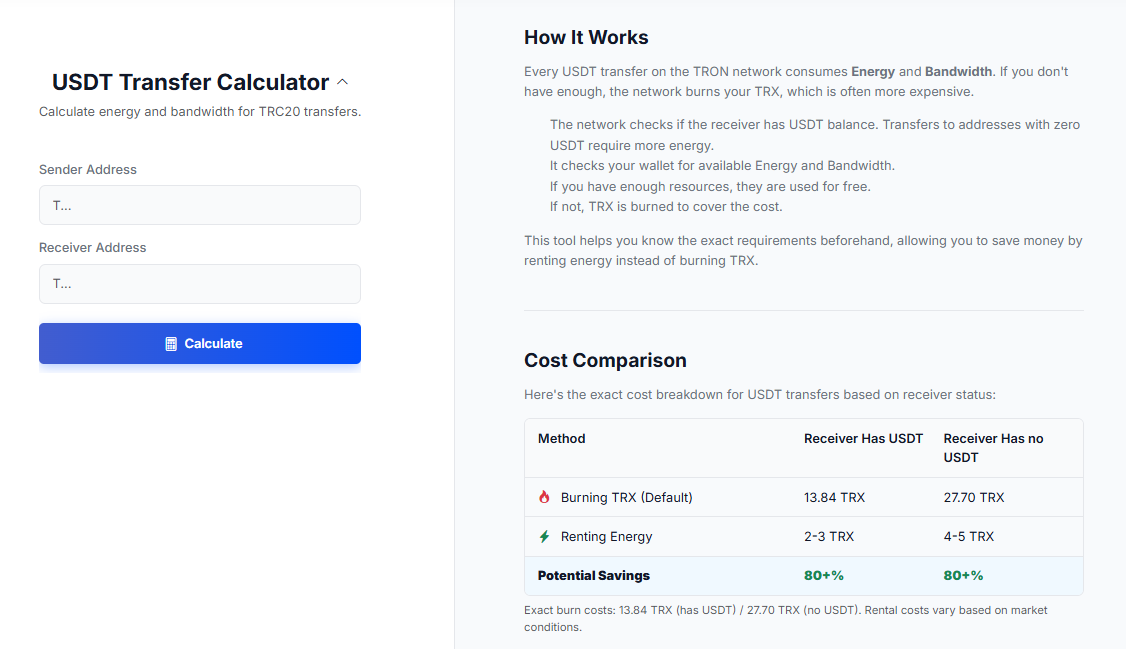
The Netts tool enables the user to enter sender address and receiver address to estimate the exact amount of resources required for sending. This reveals an important cost discrepancy: transfers to a recipient with a positive USDT balance burn about 13.84 TRX, while the burns related to transfers to a cold wallet (i.e., an address holding no USDT at all) are much more costly from the computational perspective, burning about 27.70 TRX. With this calculator (and also an API for dev), users can know if it is a good moment to rent Energy, Just so you know, renting Energy costs only 2-3 or 4-5 TRX, saving more than 80% compared to just burning TRX. This quick check ensures you're not overpaying network fees while still maintaining speedy transfers.