Crypto and Criminal Defense: Blockchain Cases
Why crypto criminal defense has been the better side of the courtroom — and why the window is closing faster than wannabe ace attorneys realize.

Many lawyers say they became a lawyer to protect the powerless, or to seek justice, or something like that: the law school graduation speech. The more real number, a smaller one, will confess after enough spirits to what they went to law for: to win cases and to cut a name for themselves. Both types exist, and both are needed. However, at all times this is a question of which side of the courtroom gives you the better odds and the better headlines, and in crypto, the answer to that question has been extraordinarily clear for the last few years. Being on the defense side has been a much better proposition. Easier to win. Easier to find clients. Better for the reputation. And far less politically uncomfortable than being the government lawyer telling a judge to please open someone's wallet.
This article is about why that asymmetry exists, what oddballs it has created, and why anyone who thinks they are planning a career on it should know that the window is closing faster than they realize.
Why the Defense Side Has the Higher Odds
In its most generous assessment, crypto law as of 2026 is a work in progress. The muscle behind it is already there — federal statutes on money laundering, unlicensed money transmission and wire fraud have all been stretched to fit digital-asset cases — but how those statutes play in crypto-specific settings is being litigated in real-time. With every high-profile criminal case comes new precedent, sometimes conflicting precedent, and the cracks that defendants can still drive a truck through are conspicuously yawning.
There are some structural features that gives defense attorneys an unassailable, more or less permanent advantage. One is the burden of proof. The standard of guilt in all criminal cases is beyond a reasonable doubt and many innocent individuals have been convicted of crimes due to the success of a competent defense lawyer creating reasonable doubts in the minds of jurors which is uniquely easy when it comes to crypto's technical complexity. It's also cryptographically unambiguous that this wallet did send that amount to this other wallet at this time on the blockchain transaction. But who was controlling either wallet, whether the defendant knew the funds they had received were criminal proceeds, whether the defendant could reasonably believe an activity he or she was being prosecuted under the statute for was a crime, and whether that activity actually fell under the statute at all — all this is exactly the kind of confusing human question that juries are notoriously bad on, and bad juries typically acquit or hang.
The next characteristic is anonymity layer. However in a traditional financial crime, an investigator can easily link to a named person via the bank in which the transaction was conducted. Yes, a wallet is just a string of characters in crypto. Connecting a wallet to an individual demands independent proof — a record from the exchange that was subpoenaed, a device on which the defendant bragged about the address, a social media status where someone said that the owner of the address is user X. Sometimes that evidence is strong. Sometimes it isn't. When it is not, a defense lawyer who reads months worth of articles on blockchain forensics can almost always come up with counter hypotheses about who controlled whatever wallet the prosecution hasn't doted on.
The third attribute is jurisdictional murkiness. It is a crime that is, by design, committed everywhere and nowhere, using a decentralized protocol. Which jurisdiction's law applies? Which court has proper venue? Did the defendant actually intend to reach out and touch the jurisdiction alleging it was violated? Defense attorneys salivate over these sorts of questions, you get motions that take years to litigate and could derail a case entirely.
Prosecutor's Problem
On the other side of the courtroom, prosecuting crypto cases appears to be less like practicing law and more like an archaeological dig through a medium no one understands. That means — even to jurors who might not know what a private key is — the government has to convince them that someone intentionally committed a specific crime. The evidence can be supertechnical. Your defendant witnesses are often also individuals mired in the same community fringe as the defendant; they can be damagingly undermined with a couple of questions about their own trading.
Mental state is the most challenging component. For the vast majority of federal crypto charges, the government must show the defendant appreciated their conduct was illegal, or at the very least criminal. Sometimes, in a space where the legality of half the activity is still being figured out, "I thought it was legal" isn't a moronic excuse; it's true. If you published some open-source code in 2020 but downstream use of that code is declared illegal in 2026, a developer might be able to reasonably argue that they thought what they were doing was legal. This comes down to the facts, but the defense has something to work with.

Valuation is another headache. It really depends on which exchange rate you are using, which timestamp, what version of the coin that may have forked or been wrapped or bridged between chains during the period in questions, etc. By cross-examining government witnesses, defense attorneys can quickly raise questions about the soft dollar figure on the government's chart. A weak number for a juror who doesn't already think the defendant is guilty chips away at confidence in the entire case.
Next comes the sheer velocity of tech change. A statute written in the '80s, interpreted through case law from the '00s and inflicted on behavior from 2022 using forensic techniques devised in 2024 will have some enough connective-tissue weakness somewhere in the chain that a zealous defense attorney can snag it. The burden is on the prosecution to get the whole chain to hold. The only thing they have to do is break the chain somewhere.
Famous Wins and Reductions
A series of cases in recent years embody the defense-side edge.
Roman Storm, one of the founders of the now-defunct Tornado Cash privacy mixer, was slapped with three federal counts: conspiracy to launder money, conspiracy to violate sanctions, and running an unlicensed money-transmitting business. A jury convicted him in August 2025 on the money-transmitting count, but was deadlocked on the two more serious charges. He is set to be retried on the open counts in October 2026, and could receive forty years behind bars if convicted on both. While the saga isn't finished, the current playing field — one count of a conviction, two hung counts, years of pretrial motion skirmishes, and a widespread failure within the legal sector to reach meaningful consensus on whether the mere act of publishing code even satisfies the requisite definition of money transmission — is surely a mixed bag relative to the government, who didn't exactly anticipate a protracted legal battle here. For one, the defense team asked real questions about developer liability, First Amendment protection for code, and whether money-transmitter statutes even applied to non-custodial software; and at least some jurors found at least some of those arguments persuasive.
Changpeng Zhao of Binance is a whole different version of the winning defense. Confronting the largest crypto enforcement action in history, according to the government — a $4.3 billion settlement that also included admitting to personal crimes related to anti-money-laundering laws — his lawyers swayed them to recommend a four-month sentence in 2024 rather than the three years prosecutors asked for. Although the case did not end with an acquittal, the difference between what the government sought and what the defendant received was, by industry measure, a substantial defense victory. Offering a straight plea, broad cooperation with framing that left Zhao with his dignity and reputation intact, then submitting a sentencing that stressed the gains changed at Binance (rather than the conduct that led to the underlying investigation).
Richard Schueler (or Richard Heart as he is known to crypto markets), the founder of HEX and PulseChain, had an SEC enforcement action initiated against him, which was entirely dismissed in 2024 — the only complete win for the SEC in any major crypto enforcement case, according to the law firm that represented him. The dismissal was on jurisdictional and pleading grounds and not on the merits of the underlying projects, illustrating the re-occurring theme in crypto defense, that the government's theory of the case, even when the factual allegations seem bad, is vulnerable to a technical attack that a well-funded defense will doubtless find.
You also have the counterexample, which can also be quite instructive. In 2024, Sam Bankman-Fried was sentenced to twenty-five years in prison for the collapse of FTX. His defense has been roundly panned — he testified against the advice of the vast majority of observers, he stumbled on cross-examination and he never wrapped together a coherent alternative narrative to the basic straightforward government frame that this case is simply one of massive theft of customer funds. The lesson is definitely not that a defense is impossible in crypto cases. What is more, it is that in probably 90% of crypto cases, the defense can swing it, except where facts are truly horrible, or the defense team fails to manage the narrative with the most rudimentary of competency.
Image Advantage
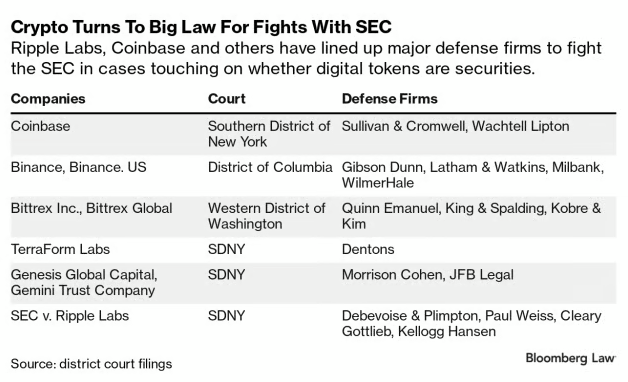
One aspect that is often not discussed as heavily in the professional calculus is reputational. When it comes to lawyers who defend crypto, they're done so, in part, as many of their clients and audiences perceive this kind of overreach — governments combing through blockchains they barely understand in search of vague, often non-existent, criminal codes to turn otherwise harmless conduct into felonies, and even sometimes targeting developers for the horrible crime of writing software. In the community, this is very nearly the moral equivalent of civil-rights litigation. Defense lawyers become folk heroes. They take the podium at crypto conferences. They build followings and they book deals and they pipeline clients.
Prosecutors, on the other hand, are made to look like the villains. The villain in the industry narrative is the prosecutor requesting from a court a compulsion to decrypt a hardware wallet, even though the underlying conduct would be widely condemned outside of a literal circle of people not holding a subpoena. This enhances the very same unfairness to the individual lawyers themselves, many of whom are doing competent, earnest work on cases where the defendants are, in fact, guilty of what they are charged with doing. Every last detail is carefully tailored, but image follows form, and the crypto enforcement structure of 2026 is one where the defense bar hard carries the glamour relative to the government side.
The amusing part is most of the best crypto defense attorneys were actually government hands. Some of the highest-grossing defense shops in the business have been created by former prosecutors who worked some of the early, high-stakes cases, learned the space back and front (and upside and downside), and then left to open practice. They bring an understanding of how the government builds crypto cases and, importantly, what kind of weaknesses the government consistently underestimates. That's a familiar cycle in specialized legal practice — financial regulators leave for banks, antitrust lawyers to defend corporations — but it is a sharper one in crypto, where the divide in understanding between people who get the tech and who don't is still so vast.
Within a defense practice serving marquee crypto clients, almost all of the operational work relates not to courtrooms. USDT, usually, with regard to retainers. In some cases, settlements require an on-chain transfer to be sent to victims, witnesses, or specific consultants. Any firm that does any meaningful amount of this work soon begins to realize that transferring TRC-20s is cheaper and faster than attempting to unwind a client’s on-chain estate every time a payment wants to go out — which is why the more technically literate practices have started learning exactly how to think about renting TRON Energy, what the best TRON Energy providers are for getting a locked quote, and how to obtain TRON Energy on such short notice that it is basically instantly available to facilitate a large transfer without breaking an ongoing client-matter escrow. This is not glamorous work but ripples through overhead in ways that smaller firms do not recognize at their own peril.
Why This Window Is Closing
The days of all of this will soon enough be over. The defense-side advantage in crypto cases is the fact that the law, the forensic tools, and the institutional knowledge are all still trying to catch up with the tech. Those gaps shrink every year.
From the legal side, just so much precedent is building. These appellate decisions are determining what statutes apply to what conduct, specifying what forensic techniques courts will admit, and writing playbooks for the next round of prosecutions that are far more difficult to disrupt than prior ones. The Tornado Cash case by itself, whatever the result, will leave a vast body of case law about developer liability, what constitutes money transmission, and whether you can apply sanctions statutes to permissionless protocols. That also means that once those questions are resolved by courts, a defense attorney can no longer say that the law is murky. Now that everyone agrees there is a rule, they will need to persuade a judge that their client[s] specific conduct [does] not fall within it, on the merits.
From the investigative side, blockchain analytics firms have seen their own maturation cycle over the last five years. Federal investigators are now equipped with common tools to trace funds across chains, cluster wallets by behavioral patterns, and identify individual actors from operational metadata. A new iteration of the old defense argument — "the government will never be able to prove my client was the one who controlled this wallet" — is increasingly difficult to make in the face of a twelve-step chain of inferences, each of which is strong on their own, which when combined lead to a credible identification. This used to confuse juries. They are less confused now.
At the institutional level, you are going to be seeing a great deal more fluency with prosecutors, judges. Last time, a federal judge in 2020 could have a basic primer on what a block explorer was; now, at preliminary hearings, they will now casually reference lightning networks, time-locked contracts and how a typical exchange hack unfolds. The information asymmetry that historically exploited defense attorneys is disappearing, and with it the comparative advantage of the defense side.

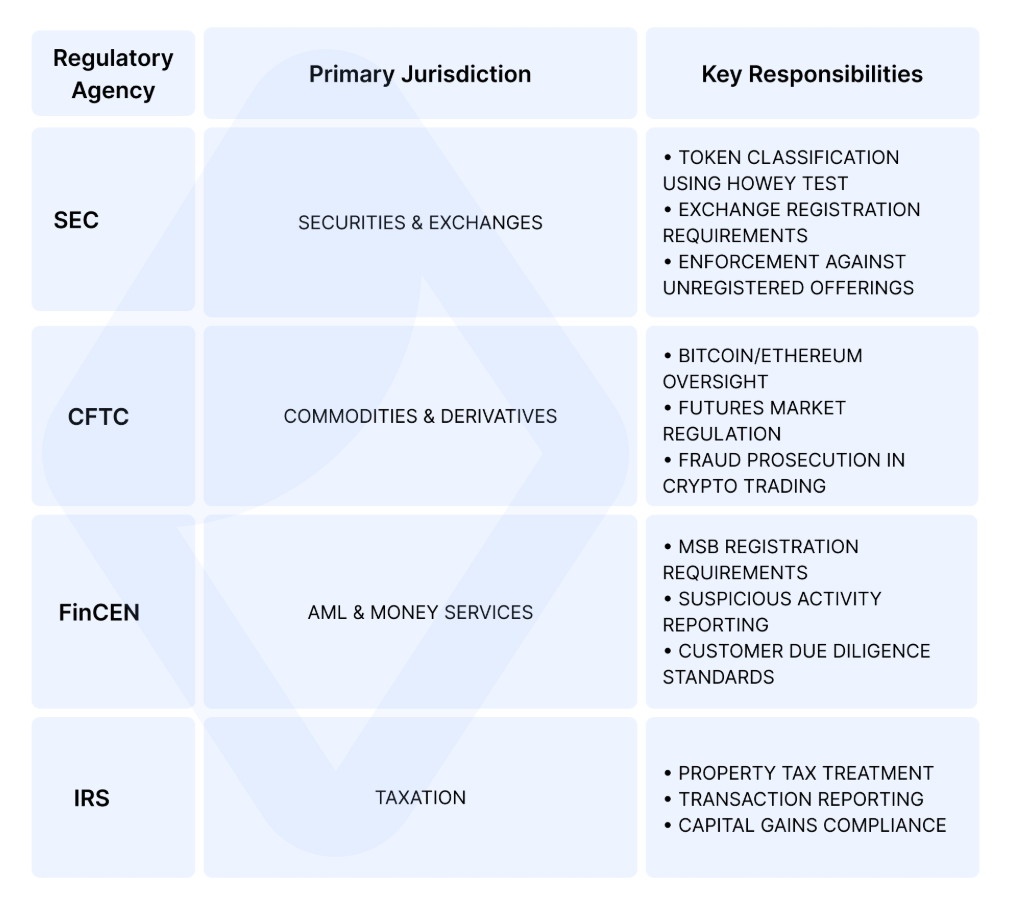
At the same time, regulatory clarity is constricting defense opportunities that rely on "I didn't know it was against the law" arguments. The GENIUS Act and its various state analogs, the NIST post-quantum migration framework, the FinCEN guidance that gets revised on a quarterly basis, the on-going US list of sanctioned protocols: this definitional landscape is a far more circumscribed compliance universe than what existed five years ago. A person charged with violating a law in 2022 could credibly assert that the legal status of their conduct was unsettled. In 2028, a defendant attempting the same argument will find it much more difficult, as the vagueness will have been supplanted by concrete, publicly accessible rules.
The attorneys who have made careers off of the defense-side advantage of the 2020s will have to learn to navigate this new market. A few will swivel to white-collar compliance, which means telling institutions how to stay out of the slammer. Many will transition to civil litigation where burden of proof is lower but expert knowledge is still in short supply. Others will discover that their existing book of business is sufficient to ride out until retirement. The next generation of crypto lawyers will be working in an older ecosystem in which cases come down to technical statutory interpretation as opposed to the general novelty of the field. It would be a much duller career, but likely a more secure one.
The larger point here is that crypto criminal defense in 2026 is basically in its own 1920s, in the lawless era when invention outruns regulation, when individual lawyers can become national names through speed of technological comprehension, and where the government is working with a short deck. This has happened in every subfield of law. Neither of them sticks with it long. The smart practitioners are already strategizing what they will do in the decade after the rules are generally settled.
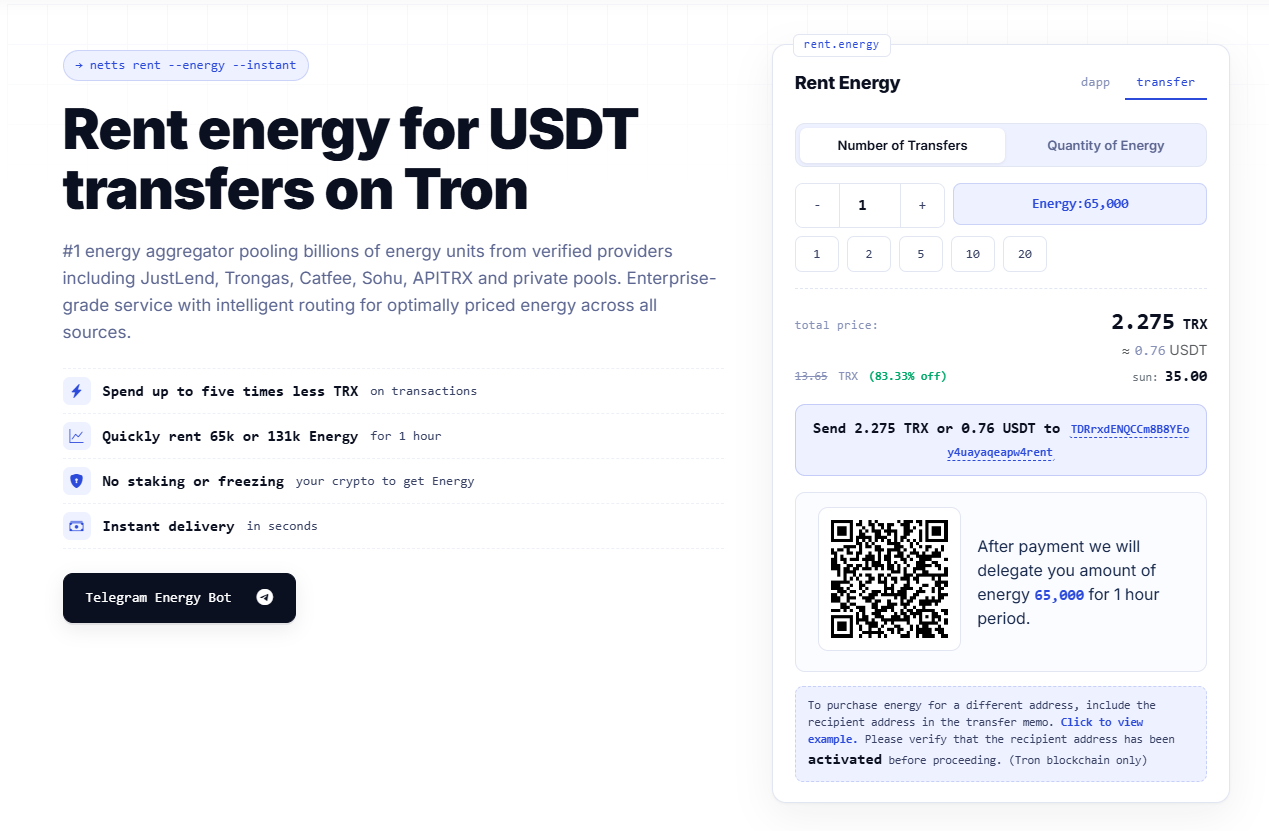
All of that is of no immediate consequence when it comes to the operational side of actually running a practice that is adjacent to crypto, which still needs to do USDT on the TRON network, with a fair amount of efficiency. Netts operates an energy-aggregation service, which integrates energy from verified providers — JustLend, Trongas, Catfee, Sohu, APITRX, private pools — and automatically routes every transaction to the most cost-effective source. This means around 80 to 90% savings over just burning TRX, delivered in just a few seconds and at rates as low as 27 sun per Energy unit at the level of the aggregator. It is the kind of infrastructure that takes a potentially constant source of friction — such as a law firm running scheduled settlement payouts, or a solo practitioner who sometimes has to handle a big USDT retainer — and turns it into a background process that no one ever has to think about. And that — at the level of actually running a practice — may be about the most honest account of what a good infrastructure is meant to accomplish.