Quantum Computing and Crypto: The Clock Is Ticking
Where quantum computing actually stands, what it means for Bitcoin, and why the cost of ignoring the threat is asymmetric.
Quantum computing is one of those subjects that gets romanticized in both directions. On one end of this spectrum are breathless predictions of machines arriving in "within a decade," that will render "all we know of modern cryptography irrelevant" and "shake our already fragile digital society to its core." And, on the other, an almost institutional quality of cynicism (dirt cheap considering the costs associated with the university as plaything in grant dollars and vaporware displays) towards a field that has promised for more than two decades to get to the station commercially but never even gets off the platform. But as often, the reality is in between those two extremes and for crypto holders in front of us, the question has transitioned from an academic one to one of sheer operational urgency, not because the quantum doom is here today, but because the timeline has unexpectedly shrunk in manner we probably would never believed only a year ago.
This article will attempt to stay off both the band wagon or the dumpster. In summary: quantum computing is real, quantum computing is still quite limited, and quantum computing is moving way faster than nearly all its own engineers were publicly predicting. And for more than 10 years, crypto networks have known about that very real risk, only recently beginning to act on it. The only question is "how quickly are they going to move?"
Where Quantum Actually Came From
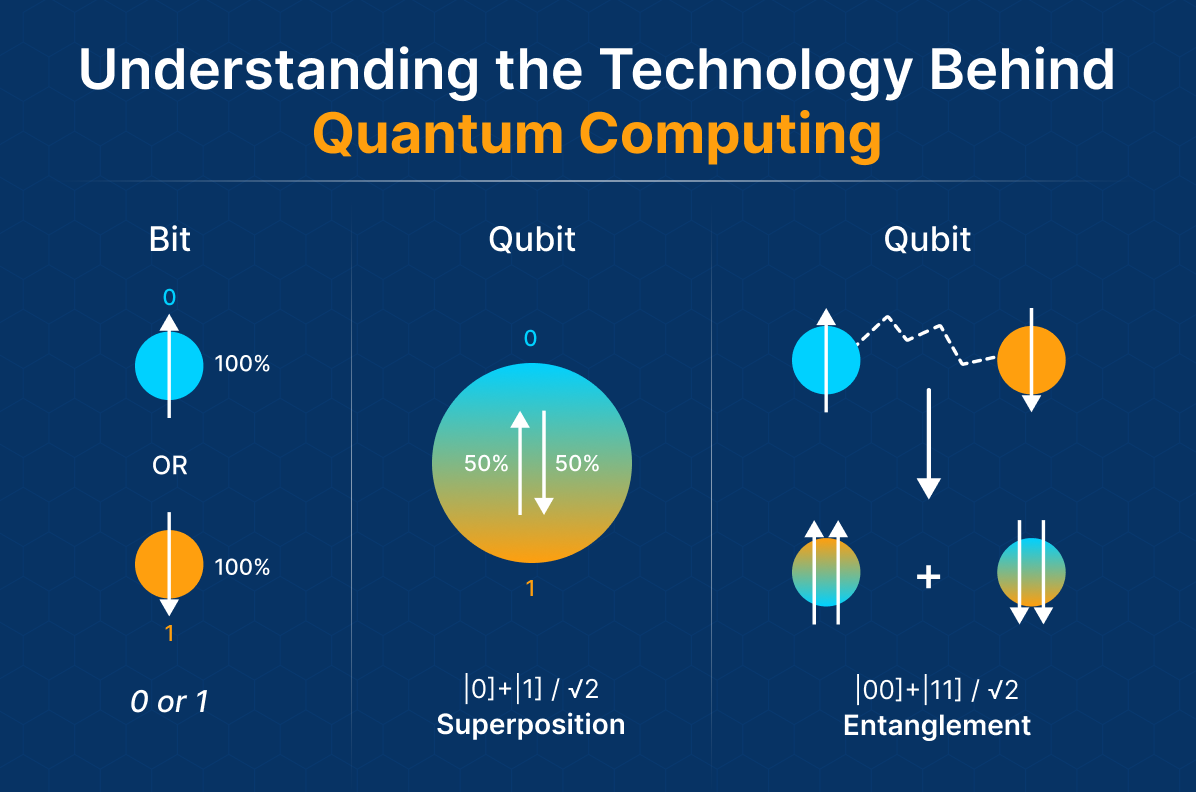
Some four decades ago Richard Feynman doodled the idea of a quantum computer into 1981 lecture notes (one would not blink if the notes were read today). But his observation was limited, and significant: classical computers are appallingly poor at simulating quantum mechanics, because quantum systems simply not capable of being represented in classical bits of information.
The response, he says, was natural because well of course if you want to do efficient quantum systems simulation of any complexity you have to build a computer out of what you were trying to simulate. This was a hypothetical suggestion that had languished in the weeds, the type of thing physicists speculated over coffee.
And that changed twice, after new developments. When Peter Shor published his algorithm in 1994 he showed that sufficiently large quantum computers can find large factors in polynomial time — a result that would make RSA, the encryption behind much of the modern internet, trivial to break on such a machine. Then in 1996, Lov Grover announced that he had a quadratically faster algorithm to solve search problems (there are also consequences for symmetric cryptography, but less serious). These results suddenly brought into sharp focus the question of whether anyone could build any of the hardware at all or were they simply just able to model it profusely on a whiteboard.
Progress has been slow and inconsistent. Although there were many experimental groups building qubit devices for the vast majority of its existence, the qubit remained a laboratory curiosity for most of the decade of the 2000s, and most of the 2010s, etched physically in some material (atom, or electron, etc.), cooled down to a temperature virtually approaching absolute zero, and instantly disturbed by any change in the environment. But the 2020s are a different matter. In September 2025, Caltech was running a 99.98 percent accurate neutral-atom quantum computer containing 6,100 qubits — around sci-fi numbers for the time two years ago. Neutral-atom systems had taken a few systems to 10,000-qubit arrays by March 2026, in some instances. IBM announced plans to get to quantum advantage by 2026 and scaled, fault-tolerant systems by 2029. If better performance was promised shortly, this had already existed: these qubits to factorize elliptic-curve cryptography (some work here, of course, done by Google) could, in principle, be running on less than half a million physical qubits and in under minutes (about a twentyfold improvement over past projections).
None of these steps amounts to a working cryptography-breaking machine. There is still quite some distance between a 10,000 qubit array and the sort of error-corrected logical system that could possibly run Shor's at scale (logical qubits typically require thousands of physical qubits each, depending on error rates and architecture). However the travel direction is no longer ambiguous, and also more or less all the people who were fobbing off the quantum-threat forecasts only by rolling the eyes are no longer rolling the eyes.
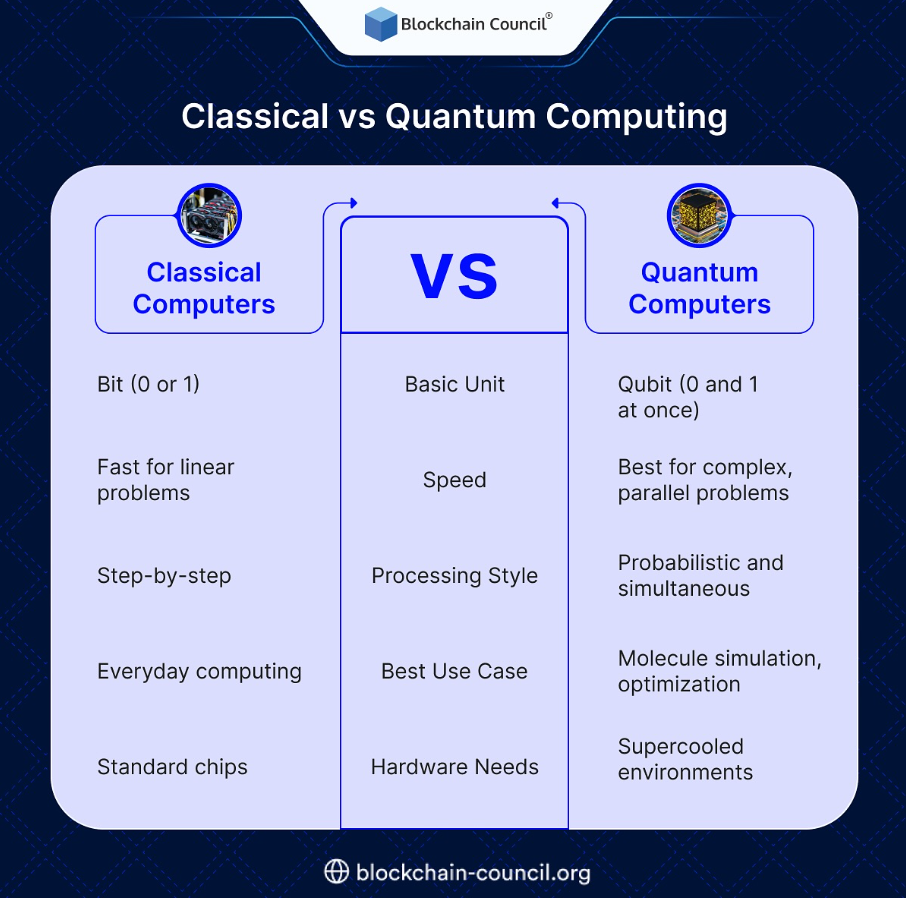
Why Crypto in General Is Getting Targeted
People when talking about quantum attacks on crypto mostly think of two things. Just like that of the public-key cryptography to protect the wallets on the blockchain — the one that nearly all the traditional chains — Bitcoin, Ethereum — uses is some type of elliptic-curve digital signatures. Second is the transport layer encryption that keeps all that traffic between users & exchanges in-line, the same encryption that keeps all but the most parochial communication on the internet somewhat private. Patches for both are in the works (in theory at least, both are vulnerable to Shor's algorithm).
On the wallet level, it actually has a certain taste of the problem. When you send a USDT transaction what happens is your wallet signs the transfer with a private key and the matching public key ends up exposed on-chain. In a world with quantum computers, an observer of the blockchain would be able to recapture the private key and empty the wallet before the transaction has confirmed — a chain-signature level man-in-the-middle attack. Before this point, there were relatively safe addresses that had never been spent from — those where there was only a hash of the public key exposed — and addresses that had previously been used that necessarily still had their public keys exposed. A quarter of global Bitcoin resides in wallets whose public keys are exposed on-chain; a number of those coins are the earliest dormant coins that may be the property of Satoshi Nakamoto. And what if the addresses are, in the end, drainable — the price implications alone are practically impossible to hedge.
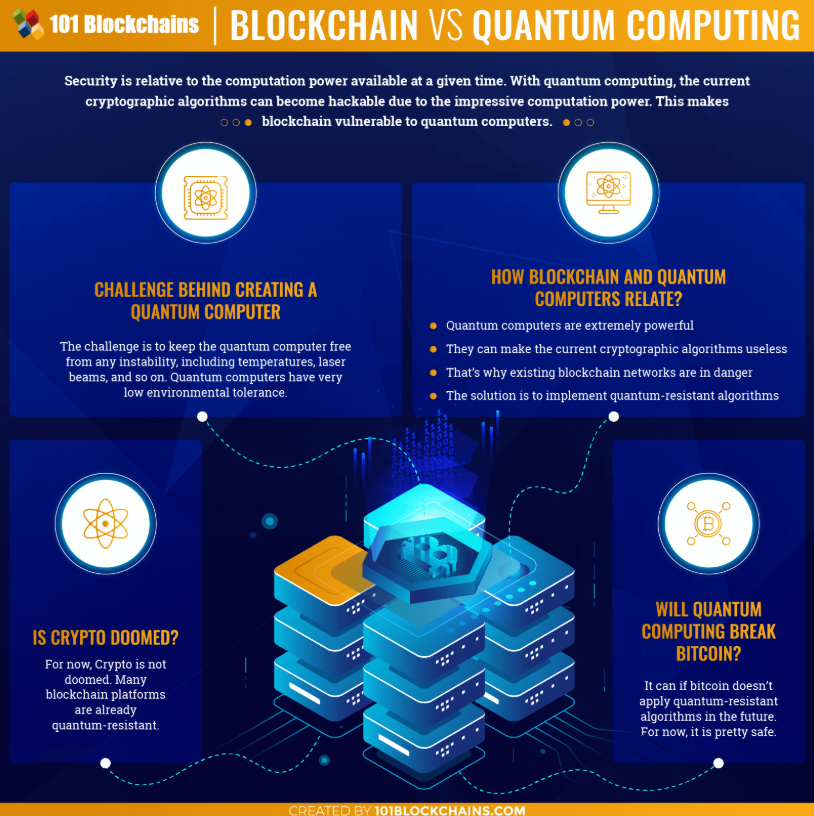
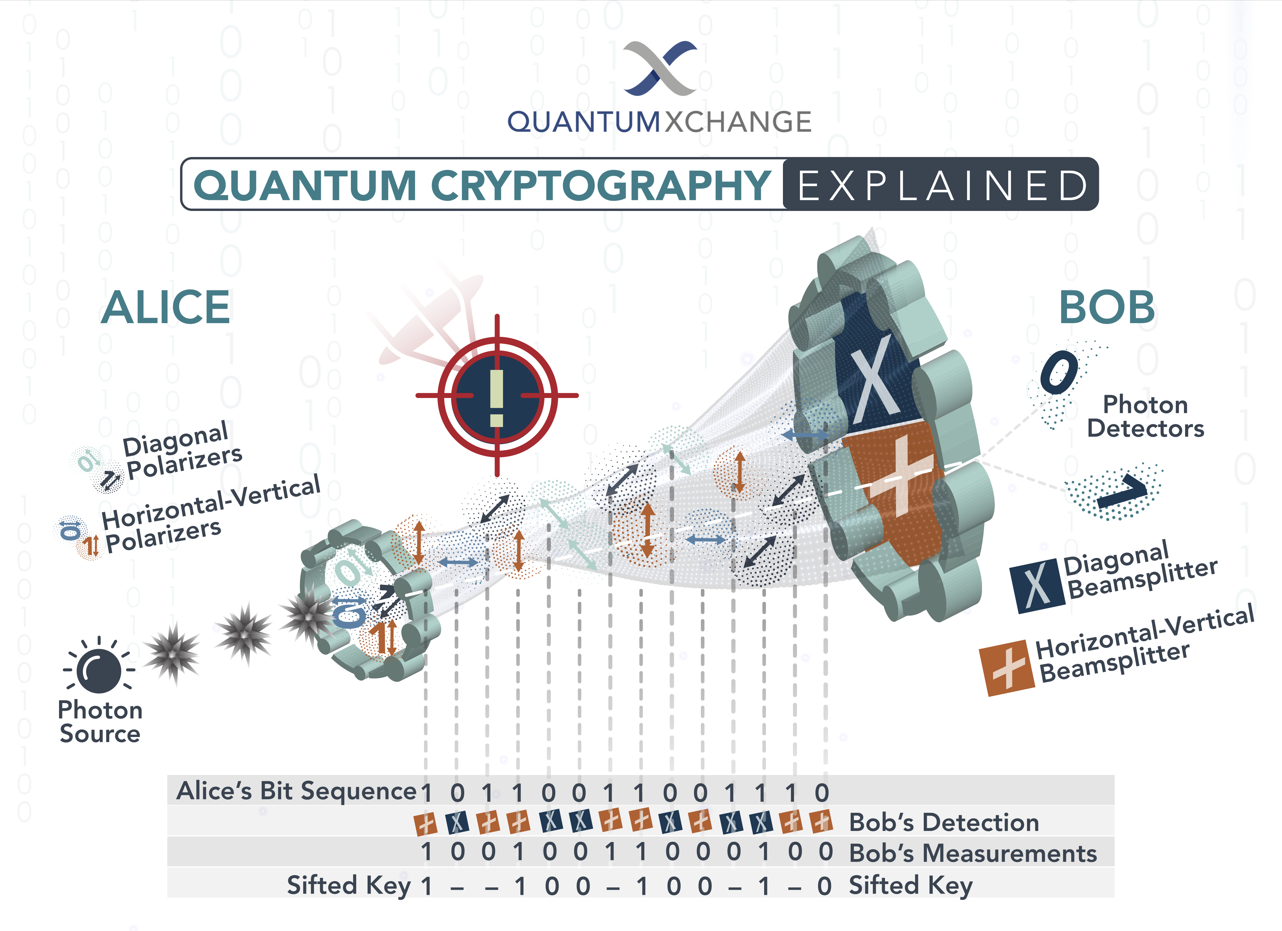
The threat can also be preemptive: the so-called harvest now, decrypt later. The theory is simple: if adversaries currently don't have a working quantum computer and therefore need not for now worry, simply key log all traffic they encounter, and decrypt whatever it is when such a machine becomes available later down the line. Most of the time it matters less for the day to day USDT send operations, because the content of the transaction is public by inherent design. And we are talking about everything that is transport layer encryption dependent — exchange login sessions, wallet recovery flows, private-key material in-flight — and this is mass destruction. Many national agencies covertly treated harvest-now as an active threat model years before there was any such thing as a conflict capability.
Doomsday Camp
The most extreme position in the debate considers quantum computing an extinction level threat to the world of cryptocurrency as we know it. It goes something like this. Blockchains were built upon a premise that the cost of compromising a cryptographic primitive was always so high that it was economically impossible to try. If that premise falters, the entire incentive structure goes down with it. Transactions become unsafe to broadcast. You cannot defend a wallet forever, because there is always an opponent with stronger source hardware than yours. All the value that was captured in the system that had previously incentivised that self-reinforcing network effect on which their entire confidence in the system was based is wiped, and the assets that were classed as being worth a certain number of tokens drastically fall on their way out of the system.
The most diehard believers in this narrative say its natural destination is a move to a hard store of value. Gold. Cash. Real estate. Commodities. Things you can hold. The narrative they tell is of an entire twenty-year-long experiment in decentralized digital money that reads like transitional technology, like a dot-com-era utility that was good only until someone put a layer on top. The mayhem in financial markets is not some theoretical case — trillions of wealth wiped out, digital infrastructure confidence totally eroded, regulators and institutions abandoning all things ECDSA or RSA based at breakneck speed.
This is a reasonable stance. This makes this scenario quite plausible, very much real if the quantum computers of the requisite size become available in 5 years time and the move to post-quantum cryptography has not happened by that time. What might be overdone is the detail. Quantum threats are not limited to crypto. If public-key cryptography fails universally, so then do the banking system, the internet transport-layer security for the financial industry, governmental communications and with it, nearly any authentication within the modern economy. Targeting in on Bitcoin as the single victim actually misses the scope — and ironically also underestimates the comparative suppleness of crypto networks, that update through factual consensus versus banking systems cast into ontology and regulatory undergrowth where it will not matter what the accelerant is for a decade to come.
Spear and Shield Camp
Another camp has suggested that it is a question of inverted framing of the conversation. The threat is real. And although the threat has been genuine, it is one that the response has in many respects been one step ahead of. In 2024, the U.S. National Institute of Standards and Technology published its first post-quantum cryptographic standards: FIPS 203 for key encapsulation, and FIPS 204 and 205 for digital signatures, respectively. One additional standard HQC was rolled out in March 2025. They are standards, not science projects, and they are weaving their way into banks, cloud providers and governments now. The federal timeline targets removal of quantum-vulnerable algorithms from compliant government systems by 2035, with high-risk systems moving much earlier.
Software is much easier to upgrade than hardware or paper law, which is an important fact that crypto networks have the ability to use to their advantage. Ethereum has made highly publicized statements of their intentions to bring post quantum signature schemes as upgrades to their protocol. Coinbase was working out a migration path plan for their custody systems on gradual basis. These are currently being explored by Solana. There is already a family of those (testing the water) quantum-resistant chains such as QRL. The series of architectural steps are straightforward; Include more address types based upon post-quantum signatures, incentivize the shift of funds over to these new types and deprecate the old types in due course.
This is mostly because Bitcoin is the hard one; the governance model behind Bitcoin is one built not to change quickly. Not if a chain takes 2 years to even reach consensus on a block-size upgrade. Historically, optimists may note that Bitcoin has had complicated soft forks in the past and that if it were a serious threat then the community would likely band together as one. You were already exposed by the time discomfort lands — as pessimists point out, "in the face of a tangible threat" is always, by definition, too late (the harvest-now-decrypt-later dynamic). Regardless of who wins that debate, even Bitcoin agility nonbelievers acknowledge that the underlying technology allows for changing if there is social agreement.
What this camp reminds us of is that where there's a spear there's usually a shield, and where the spear is being forged in the crucible of public opinion over decades, the shield has had time to be forged right alongside it. It cannot be ruled out that quantum cryptography itself — quantum-key-distribution systems that exploit the physics of measurement for security — will one day also fall into the fold, too, not just post-quantum math operating on classical machinery. In theory, a world where every USDT sent is backed by quantum-resistant signatures, and encrypted against harvest-now attacks by default, is already within reach. The existential question is whether we are going to make it before the apocalypse comes.
"It'll Never Happen" Camp
Less fashionable than even a few months ago but nonetheless alive the third position is that general purpose, commercially useful quantum computing is a moving target. Supporters point out that the sector has been on the brink of a reversal since the 1990s. Those qubits which are usable, however are exceptionally costly and fragile. That is, error-correction overhead — different depending on architecture and error rates and sometimes nearing 1,000 physical qubits regardless for a single logical one — pushes the hardware needed to actually break practical cryptography into a rolling deadline, just out of reach, again and again. That most of the high-publicity multi-year "breakthroughs" of the past decade are curated showcases chosen to deliver quantum superiority on limited first-world problems, not signs of general-purpose quantum computing being on the horizon.
The analogy it tends to reach for the most — is flying cars. A technology that was credible in the 1950s, had real-world prototypes in every decade since, has been commercially imminent for just as long, and has, in any useful sense, yet to arrive. It is not that flying cars will never be a reality — it is the reality that the gulf between "the physics works" and "it is on the market at a price that matters" can actually be arbitrarily large, and a huge amount of institutional inertia is quietly subsidized on the belief that the gap should eventually close, regardless of whether it even does.
Such an assertion may seem counterintuitive at a time when recent evidence would suggest otherwise, but in many ways this view merits more serious consideration. State(-funded) hype exists because state funding depends on it. Press releases citing qubit counts say nothing about whether those qubits can actually perform computations of any meaningful depth. The distance between a lab demonstration and a production system can be many orders of magnitude and decades — sometimes both. So as each year passes, it runs far too often now (increasingly?) too quietly moved back each year the one dimension the quantum-threat clock gets moved forward, and the media reports on the forward-movement only.
But the classic it'll never happen (in this case, specifically with regard to crypto) is miscalibrated for one thing: the asymmetrical cost of being wrong. Even if the skeptics are right, and neither a scalable quantum computer is built nor will be built, the networks that have migrated to post-quantum signatures lose a bit of coordination overhead, a bigger signature, a bit of community infighting (non-zero, yet all stuff crypto nets barely get out empty from). But if the deniers are wrong, the non-doing networks get written off. Reason, in that type of uncertainty, would say prepare, which is pretty much what the big boys have been doing but with a strong dislike.
That brings us back to the old Warren Buffet conundrum of foggy front windows and clear rearview mirrors: you can't see into the future and eventually you can't miss the past, and only time, whether in the form of machines on doorsteps, or not, will elicit the last rage in both camps. As of now, the most likely approximation of consensus across researchers is probably a less than 10 percent probability (by 2032) that a quantum computer can recover a real-world Bitcoin private key — but steadily increasing probability through the 2030s. Not really a bold prediction there, as well; rather a distribution — the kind you get when first-order factors in your statistical model include experimental physics, supply-chain engineering, national-security funding priorities and the random walk of algorithmic progress. Anyone who says anything more specific than that is a vendor.
The recommendation that endures in any eventual outcome of the camps is merely hygiene on the part of the user. Use fresh addresses when possible. Avoid reusing old addresses, especially for large balance transfers. Track the post-quantum migration path that your chain of choice targets. To the degree that you are doing thousands of transactions per day (the usual scenario for anyone managing USDT transactions at scale), the marginal cost for applying good hygiene is minimal, and the upside of being in a post-quantum address when that time comes could be enormous. USDT transactions on TRON are not without their own optimization logic, from an economics point of view, long before quantum computers even enter the stage.
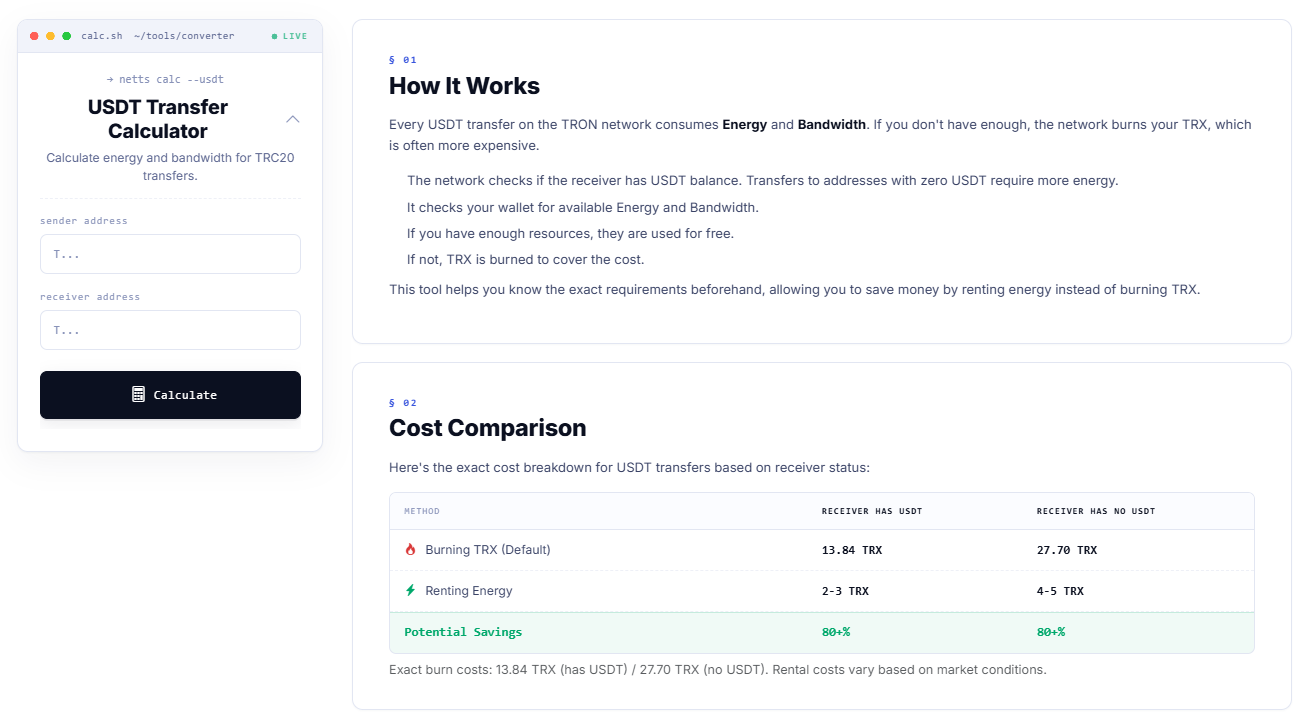
The USDT Transfer Calculator from Netts tells you, before you broadcast, how much each transfer actually costs in Energy and Bandwidth and whether the network will charge you by burning TRX or allow you to cover the cost with rented resources instead. The numbers are straightforward: burning TRX by default for a transfer to an address already holding USDT costs 13.84 TRX, while sending by default to an address that does not hold USDT costs 27.70 TRX; renting Energy brings that down to 2–5 TRX in both cases, with typical savings over 80 percent. Practical optimization is the type of optimization that is basically independent of quantum physics and has everything to do with literally not burning USDT on each USDT send, one transfer at a time.