Science of Crypto: What Papers Made it All Possible?
From al-Kindi to Shannon, public-key crypto, and zero-knowledge proofs — the research lineage behind every wallet signature and block your phone confirms.
Blockchain had exploded on to the mobile screen long after the polymath Abu Yusuf Yaqub ibn Ishaq al-Kindi produced his manuscript On Deciphering Cryptographic Messages in the ninth century, codifying the first scientific approach for repeatedly breaking secret texts. In treating letters as data and in counting up their frequencies, al-Kindi supplied promethean spark to cryptography: the demonstration that systematic observation, rather than inspired guesswork, could penetrate a concealed text.
That same spark shows up any time a crypto wallet is opened today. Every tap in John Doe’s transaction to authorize payment today invites the same algebraic mindset al-Kindi inaugurated — gather statistics model uncertainty believe math over myth. His mix of empiricism and theory helped to develop the very notion that secrecy and verification could be engineered, a basic promise that underwrites every blockchain ledger entry today.
Promethean Beginnings of Crypto Science
When in 1467 Leon Battista Alberti wrote down the description of his own cipher disk, and when Blaise de Vigenère spread his Traicté des Chiffres around him in 1586, they were not simply amusing themselves with clever tricks. They were formalizing the relationship between keys and messages, presenting polyalphabetic substitution that could stave off brute force (by hand). For the scholars of their era, that meant secret diplomacy; for a modern-day crypto investor, it presaged the revolving keys that defend exchange APIs from bots.
The next significant paper was at the end of the 1850s, when Charles Babbage used the concept of indicators and published on his algorithm; however, this was upstaged when Friedrich Kasiski's Handbuch in which he described his method of deciphering by finding repeating patterns in plaintext (a key length) was published as a book titled Die Geheimschriften und die Dechiffrir-Kunst.
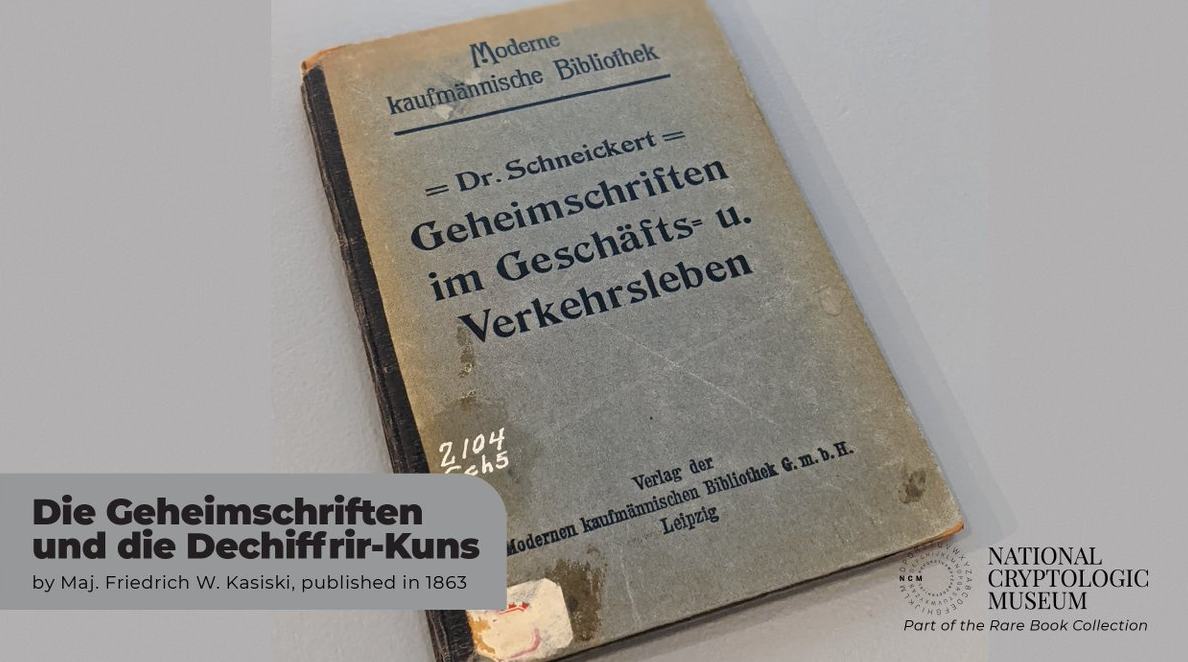
Their math said no key should ever repeat without consequences, an intuition the average crypto user is acquainted with when, for instance, a wallet tells them not to re-use their password or seed phrase.
In an 1883 essay, La Cryptographie Militaire, Kerckhoffs argued that a cipher should be secure even if everything about the system is public — except for the key. That maxim reverberates through open-source smart contract culture, where auditors and white-hat researchers put their code out for all to see so security comes from keys and math, not obscurity.
Statisticians and linguists later honed these insights into curricula, as postal systems and international cables spread around the world. Practical frequency analysis was recorded by the French military cryptanalyst Étienne Bazeries in the 1890s and, on the other side of the Atlantic, Elizabeth and William Friedman established standardized educational programs that thought of codes as signals to be counted. Those programs created the expectation that cryptography would be taught, tested and advanced instead of only inherited.
From Telegraphs to Turing
As industrial disputes called for a need for speedy communication, cryptography developed in tandem with electronics. In 1917 William F. Friedman’s pamphlets from Riverbank Laboratories systematized statistical cryptanalysis, disentangling cipher design from codebreaking and bequeathing to the world the index of coincidence. The pamphlets taught analysts how to regard probability tables, a habit that echoes to this day whenever an exchange risk engine scores a login attempt.
Herbert Yardley’s 1931 tell-all The American Black Chamber was a cookbook that whetted the public’s appetite for divining secrets, while exposing intercept stations and launching the first worldwide debate over privacy versus security.
Crypto enthusiasts today re-enact that dispute whenever lawmakers debate rules requiring traceability of money on the blockchain when it is pegged to a value in the real world with stablecoins.
In the same year, engineer Gilbert Vernam filed a telegraph cipher at AT&T and in 1919 Mauborgne extended this to the one-time pad principle. And not long after that, in 1949, Claude Shannon showed that Vernam’s system gave perfect secrecy if keys were random and at least as long as the messages but never reused. Which is why hardware wallets are so sweaty about secure random number generators: without a high-entropy source, the one-time pad turns into a multiple-user backdoor.
The interwar years and World War II just happened to give us a 1936 paper of Alan Turing’s, On Computable Numbers and his 1940s work at Bletchley Park, along with Marian Rejewski’s earlier 1932 Enigma analysis. Turing’s theoretical machines introduced the idea of algorithms as mechanical processes, which in turn led to stored-program computers that perform validations of blockchain signatures on silicon. When a layer-2 rollup checks thousands of transactions through every second, it runs the sequence of Turing’s proofs on what machines can compute.
Claude Shannon’s 1949 Communication Theory of Secrecy Systems concluded this period. By placing secrecy in an information-theoretic context, he introduced notions like confusion, diffusion and entropy. Ordinary users of cryptocurrencies come across those notions when AES-GCM secures the HTTPS sessions through which they receive price feeds to their apps, or when a cold wallet won’t release a key no matter how many times you type an incorrect PIN.
Norbert Wiener’s 1948 tome Cybernetics introduced the mathematics of feedback and control, shepherding in the adaptive security modules that today adjust anomaly thresholds inside smart contract monitoring dashboards.
The machine learning defenses that are themselves monitoring for wash trading owe as much to Wiener’s feedback loops as they do to the current generation of GPUs.
Public Keys and Digital Trust
Before the internet could automate value, we needed to make symmetric ciphers that silicon cared about. Horst Feistel’s 1971 published IBM technical reports for block ciphers led to the Data Encryption Standard of NIST in 1977. DES’s per-round function and scheduling mechanism planted the seed for today’s AES tournaments, making sure that a stablecoin transaction between continents remains private within TLS tunnels.
Not long after, Ralph Merkle published his 1979 thesis on one-way hash trees and gave us the Merkle tree structure that now allows nodes to verify inclusion proofs without having to get every data block. Block headers are checked by every light client and NFT marketplace in the EVM which rely on those trees.
Then came the revolution: Whitfield Diffie and Martin Hellman’s 1976 paper New Directions in Cryptography added public-key exchange, while Ralph Merkle’s proposed puzzles supplied the missing third leg. All at once, strangers could collude on a secret over open channels. For the average wallet holder, that miracle is the handshake taking place behind every QR code scan that pairs a mobile app with a browser extension.
RSA was introduced in 1977 when Ron Rivest, Adi Shamir and Leonard Adleman published A Method for Obtaining Digital Signatures and Public-Key Cryptosystems. The algorithm was founded on the use of large primes and has since underpinned electronic signatures, software updates and SSL Certificates that top crypto trading sites renew every year. Even custody services that are putting hardware security modules in place rely on RSA and elliptic curve variants as their root of trust.
Authentication protocols matured in parallel. Encryption is one version of the solution to this problem, and it turns out that in 1978 Roger Needham and Michael Schroeder’s paper Using Encryption for Authentication proposed challenge-response flows which Kerberos tickets look a lot like, except this was a decade early. Mobile banking and centralised exchanges continue to utilize the ticket-granting methods evolved from that family tree to securely synchronise sessions.
The 1980s diversified the toolbox. Taher ElGamal’s 1985 discrete logarithm signatures was the source for both the 1994 Digital Signature Algorithm and today’s Schnorr-based multisig. In 1985 elliptic curve cryptography was independently invented by Neal Koblitz and Victor Miller, which provided blockchains, such as Bitcoin with a small signature scheme. David Chaum’s blind signature paper of 1983 and his cryptographic protocols for untraceable emails two years later are the heralds of digital cash long before Satoshi Nakamoto reinvented it.
Once DES’s 56-bit keys became vulnerable, NIST’s adoption in 2001 of the Rijndael algorithm as it gradually percolated to produce 128- and then 256-bit security for all.
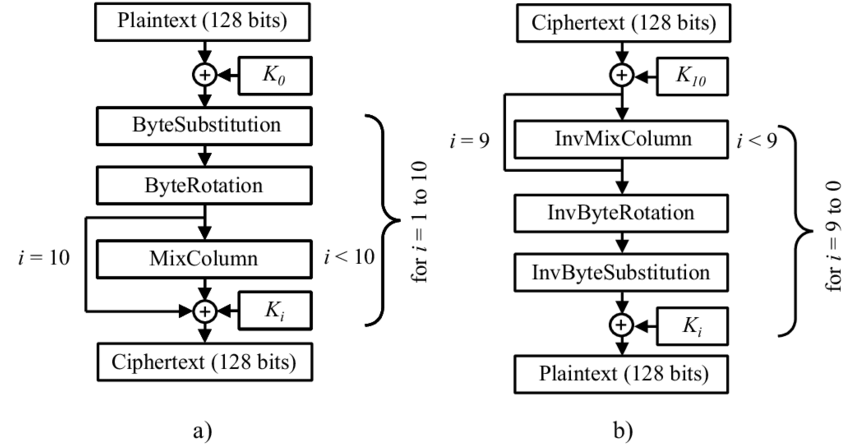
AES-GCM is now encrypting the JSON-RPC calls that wallet apps issue, a show of consumer-grade resilience that government competitions can yield.
Theory had caught up with consumer software by the 1990s. Phil Zimmermann’s Pretty Good Privacy package in 1991 brought end-to-end encryption to personal computers, and the same year Paul Kocher published a paper for Bellcore that exposed timing attacks requiring hardware designers to mask side channels. Proof-of-work as an antispam measure was formalized by Adam Back’s “Hashcash” in 1997; it only later evolved to protect decentralized consensus. Meanwhile, Cynthia Dwork and Moni Naor’s 1992 pricing via processing paper was a preview of the fee markets that every crypto trader plays when using dapps on-chain.
Hash functions also evolved. Constant time operations were brought to modern blockchains through sensing design failures from Bart Preneel’s 1993 work on one-way compression functions, the 2000 adoption of SHA-256, and Dan Bernstein’s Curve25519 in 2005 with Ed25519 signatures following in his footsteps in 2012. BLS signatures (introduced by Dan Boneh, Ben Lynn and Hovav Shacham in 2001) have recently been implemented to aggregate validators in Ethereum’s consensus and decrease bloated messages.
These papers are more than lore; they hum in every wallet. Here are a few echoes of that sentiment in daily crypto life:
1. Tokens for two-factor authentication originate from the same modular arithmetic as Diffie-Hellman key-exchange protocol, allowing a hot wallet to securely synchronize with a phone.
2. Deposit and withdrawal pools from cold storage categories use Chaumian blinding, also relying on Lamport hash chains to reconcile withdrawals without revealing its signing keys.
3. Smart contract audits use the Kocher attack models and Hashcash style rate limits to throttle bots, ensuring staking dashboards remain responsive during volatility.
Post-Quantum Frontiers and Daily Life
And then in October 2008, Satoshi Nakamoto introduced the world to a white paper titled Bitcoin: A Peer-to-Peer Electronic Cash System — incising Merkle trees with Hashcash and digital signatures on an economy. The first genesis block went live in January 2009, and proved that economic incentives could be used to maintain a bookkeeping ledger without centralized authority. That concatenation of research still forms the foundation of each tap to verify a balance on a play-to-earn platform.
Within the same year, Craig Gentry’s thesis A Fully Homomorphic Encryption Scheme showed that arbitrary computation on encrypted data is feasible. Today, twenty years later, exchanges use batched homomorphic proofs to balance fiat ramps without disclosing customer information on counterparties. For the users, it provides a way to demonstrate solvency or income while also keeping keys private.
Secure multi-party computation came a long way since the 2011 SPDZ protocol by Nigel Smart and others, which allowed custodianship institutions to share keys among authorized co-signers. When a trading desk signs off on a large transfer, SPDZ-style arithmetic makes it so that no single employee can peddle the secret.
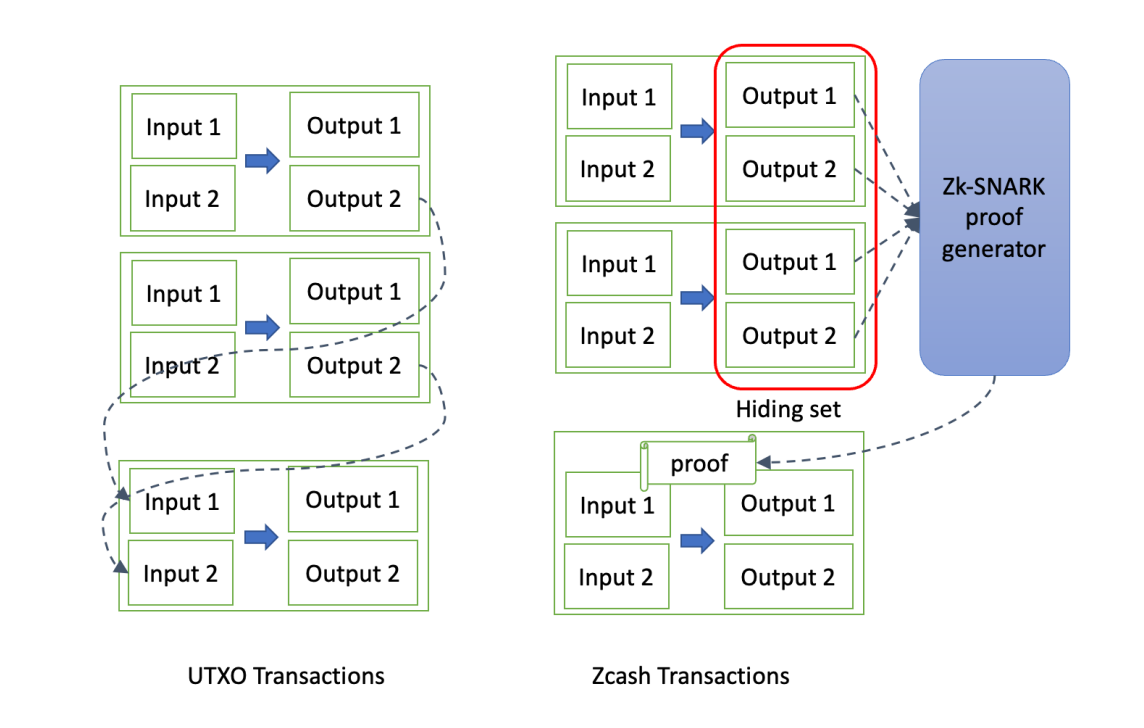
Zero-knowledge research accelerated next. The 2012 paper by Eli Ben-Sasson, Alessandro Chiesa, Eran Tromer, and Madars Virza first brought zk-SNARKs to the attention of blockchain readers, leading eventually to Zcash in 2016 and today’s privacy-preserving bridges. Mary Maller’s 2018 Sonic protocol and Ariel Gabizon’s Plonk system in 2019 lowered proving algos, making it possible for mobile wallets to perform instant verification of shielded transactions.
Logarithmic-size range proofs were introduced in Benedikt Bünz’s 2018 Bulletproofs paper, which are incorporated into privacy coins and decentralized exchanges to prove that there is enough collateral without revealing the balance. The pending adoption of Bulletproofs++ by several Layer 2 teams in 2025 will bring fast confidential DeFi trading to consumer-grade hardware.
Timely advances also tamed consensus. Byzantine fault tolerance work was refined further in the 2001 Practical Byzantine Fault Tolerance paper by Leslie Lamport, Dahlia Malkhi and others while Silvio Micali’s 2017 Algorand paper showed a way to scalable proof of stake. Ethereum’s 2022 merge — based on the 2017 research from Casper FFG — now allows regular users to stake through pooled services that stuff what were pages of math behind a nice front-end dashboard.
Layer-2 payment channels grew up in the form of Joseph Poon and Thaddeus Dryja’s 2015 Lightning Network paper and subsequent BOLT specifications. Their commitment transactions and penalty protocols are indeed simply applications of the hash timelock contracts studied in 2000, granting literal shoppers at stores sub-cent fees when they pay with cryptocurrency-enabled cards.
New urgency came with the quantum predictions. CRYSTALS-Kyber and CRYSTALS-Dilithium were chosen by NIST into standardization in 2022, with drafts of FIPS 203 and FIPS 204 circulated to vendors as early as 2024. In 2024, exchanges like Coinbase and Binance started beta-testing Kyber-based key wrapping in hardware modules; meanwhile Ledger’s 2025 firmware roadmap contains proposals for hybrid RSA/Kyber proofs so that a swap request can withstand quantum adversaries of tomorrow.
Studies carried out in 2024 and 2025 further developed the theory, realizing it and making it practical.
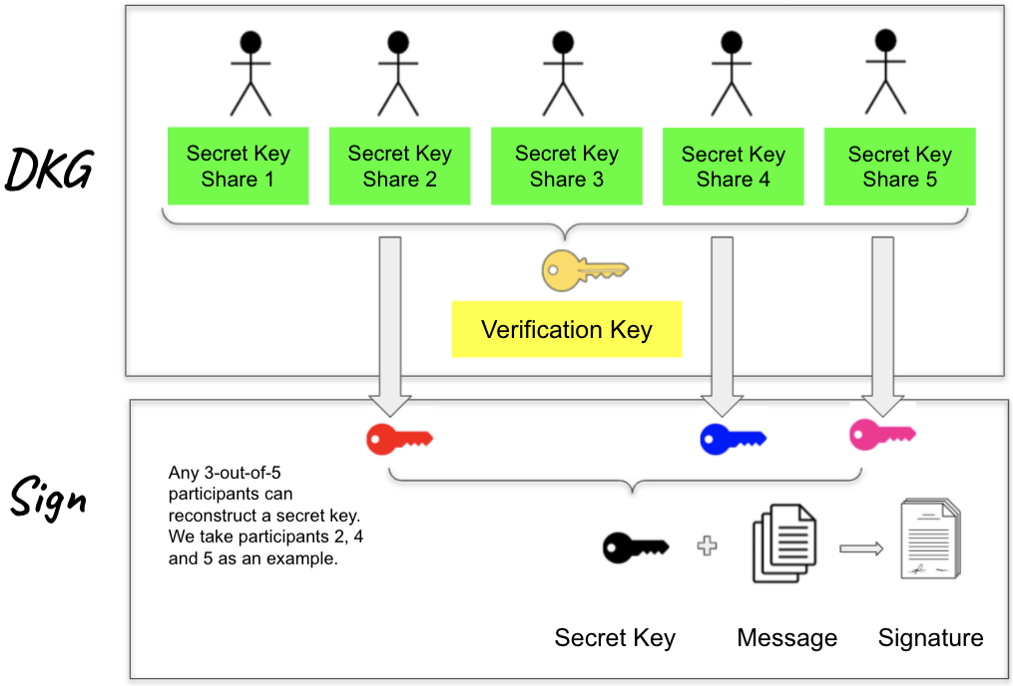
In early 2024, the FROST threshold signature scheme makes it to an IETF draft and multisig wallets can co-sign with efficient rounds. Ethereum danksharding prototypes were based on the 2020 Kate polynomial commitment paper and 2023 Proto-Danksharding spec, enabling rollups that settle payments into global ledgers for gig workers at a far more manageable rate.
The account abstraction research, where a blizzard of important details have been crystallized into Ethereum’s 2023 ERC-4337 standard and the 2024 EIP-7702 proposal is what brings smart contract wallets to mainstream users. Papers by Trail of Bits and the Ethereum Foundation put a number on bundler economics, so that we can finally get biometric signers or social recovery groups into DeFi without asking anyone to memorize seed phrases.
Today, the crypto hodler’s journey is informed by those milestones. Wallet backups are based on Shamir’s 1979 secret sharing, hardware enclaves deploy the 2016 SGX remote attestation white paper, and password compliance teams refer to the 2021 FATF Travel Rule guidance along with zero-knowledge attestations from 2023 research at Electric Coin Company. When a DeFi farmer follows yields, they are dwelling within the sandwich of formal proof, regulatory science and interface design.
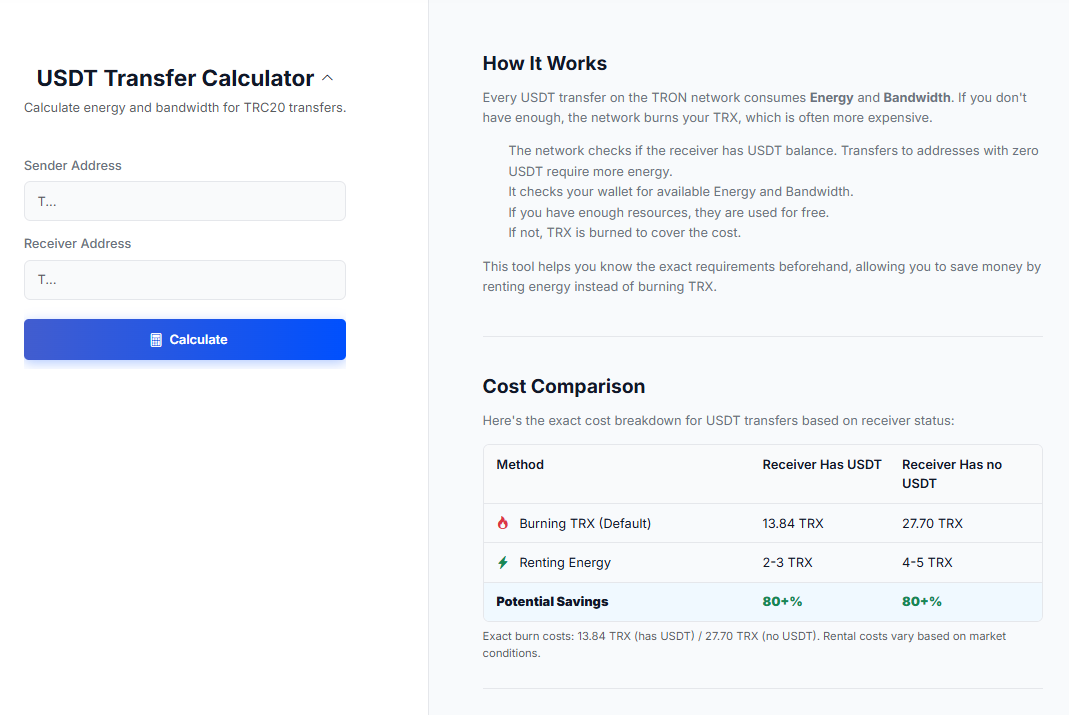
Even day-to-day tasks such as transferring USDT on the TRON blockchain lead back to those papers. Renting marketplaces for Energy which popped up following the 2018 TRON Virtual Machine paper use resource-based pricing models originally suggested in Dwork and Naor’s proofs-of-work. Those pondering whether to lease TRON Energy from a delegation pool or simply outsource it weigh pricing, delegation rules, and provider reputation when they shop TRON Energy marketplaces.
In the near future, collaborations such as the 2024 MIT/Stanford condensed block verification paper, or University of Waterloo’s 2025 research on confidential smart contracts based on lattices offer upgrading paths that non-expert traders may never directly know about. But every time a hardware wallet syncs more quickly, or a remittance herds more micro-payments into a block, it is because scholars have labored for centuries to turn conjecture into peer-reviewed blueprints.
Together, this lineage shows a straightforward truth: without al-Kindi’s statistics, Shannon’s entropy, Diffie and Hellman’s key exchange, RSA’s signatures, Nakamoto’s consensus and the zero-knowledge and post-quantum revolutions of the 2010s and 2020s — the crypto vocabulary would just be an empty gloss. Whether you can scan a code, sign a message or swap a token rests on the papers that provided confidence that each step made sense and was safe.
This article was brought to you by Netts. Netts' USDT Transfer Calculator is one of its many features, allowing you to find out exactly how much Energy you will need to rent for the next transaction: