Crypto Security Guide - How to Prevent Losses
Major hacks show even big platforms fail — passwords, 2FA, cold storage, updates, and skepticism keep users safer.

The world of cryptocurrency has been subject to a wave of hacks causing dismay for users all around the globe. One of the worst instances happened in February 2025 when Bybit, one of the world's largest cryptocurrency exchanges, became a target of an enormous hack that was reportedly carried out by North Korea's state-sponsored Lazarus Group. This hack saw more than $1.5 billion in Ethereum stolen, adding to an overall amount of over $2.4 billion lost in cryptocurrency across different coins and tokens during the same period. Thousands of the platform's users at the time fell victim to the breach, once again exposing a gaping hole in its security architecture for hackers who would get unauthorized access to those funds after exploiting gaps within their authentication systems. This serves as an unfortunate reminder that even large, well-established services can be compromised through sophisticated attacks, and it reinforces the need for security best practices to prevent people from being affected regardless of where they hold their assets.
The Bybit hack was especially alarming because it showed how attackers could circumvent multiple layers of security via a combination of social engineering and technical workarounds. There were also user accounts that had two-factor authentication turned on and who kept their details safe from such simple hacks, yet still fell victim to the portal's internal security collapse. This episode unfortunately shows just why diversifying one's storage methods and continuing to control your own private keys are still so important in the world of crypto. And the episode spotlighted the difficulties of having those stolen funds recovered in a decentralized (i.e. there's no bank to turn to) world where transactions, once finalized, are more or less final.
The 2025 Bybit incident was not a one-off. During just the first half of the year, over $2.47 billion has been lost to crypto hacks and scams — that's a 3% increase from last year. These are mind-blowing statistics yet they illustrate the increasing risks in crypto and the need for everyone to follow best practices for security. This has never been as true as in today's world where attacks have become more and more prevalent and sophisticated, and every user and platform is a potential target for a breach.
Every user, no matter how experienced or how large their investment, needs to understand the basic security principles that they use to protect cryptocurrency. Cryptocurrency crimes illustrate how decentralization of financial systems could mean ultimate responsibility for losses is assumed by the users rather than institutions as in bank fraud protection. Specifically, this task demands not just the knowledge of an array of potential threats but also the necessity to put in place multiple defense technologies and concepts which in combination will give you true shielding against multifarious attack vectors.
Because transactions cannot be reversed, and because cryptocurrency funds are pseudonymous and can easily be transferred across borders, it has become a prime target for cybercriminals. Typical threats are phishing attacks that trick users into disclosing confidential information by posing as a reputable party, malware and spyware programmed to remotely control computers or devices and steal private keys, hacks of centralized exchanges featuring loss of user funds, and smart contract bugs exploiting flaws in decentralized applications, leading to money draining. Early detection of these threats is the basis for efficient countermeasures.
Key Security Practices for Everyone
Several straightforward, but important techniques should be used by every user to establish a foothold in cryptocurrency security. Good passwords are our first line of defense against unauthorized access. Such passwords should use a mix of upper and lower case letters, numbers and special characters - which should not relate to easily guessable information like birthdays or common words. Password managers can create and store such strong passwords, relieving you from the effort of remembering several strong passwords and guaranteeing that each account has its own password.
Two-Factor Authentication (2FA) provides a second layer of security that ensures your accounts stay protected even if your passwords are compromised. SMS-based 2FA does offer some protection, but authenticator apps are preferable due to being less prone to interception and social engineering. Hardware security keys are the ultimate form of 2FA, giving you a physical token that can't be duplicated or intercepted from elsewhere. For users, they should turn on 2FA for all cryptocurrency-related accounts including exchanges and wallets or any platforms where the asset is being managed.
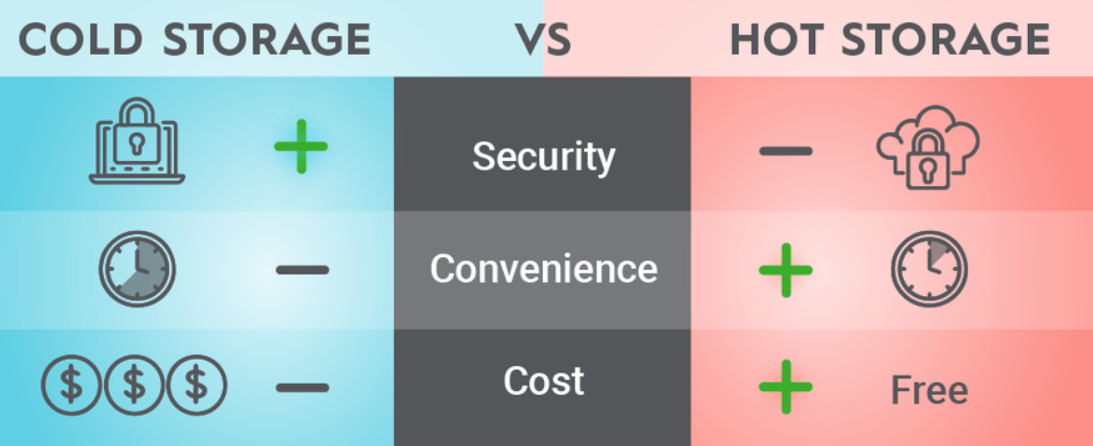
In general, wallet safety is the basis of cryptocurrency protection and wallets differ in their security. Hot wallets that are still connected, however convenient for everyday transactions, also bring those users closer to online threats. Cold wallets, such as hardware and paper wallets, keep private keys offline, thus almost completely secure from remote attacks. It should be the user's needs that dictate which type of wallet to use: cold storage for larger, long-term holdings; hot wallets are friendly enough if you conduct more frequent trades but with less capital on hand.
Frequent upgrades also mean that users take advantage of the newest security patches and vulnerability resolutions. Not just wallets, operating systems, and web browsers - any piece of software that is used to access cryptocurrencies in some fashion. Attackers often take advantage of known vulnerabilities in legacy versions of software, meaning frequent updates prove to be a simple but effective way to protect yourself. While automatic updates should be turned on if they're available, users would do well to manually check for updates on any of their most important apps.
Preventing phishing attacks is a constant exercise in attention to detail and distrusting of unbidden communication. There are now more sophisticated phishing attempts out there where you might receive an email, supposedly from a reputable company with the right branding and everything calling for some information through a form. To stay safe, always double-check URLs and look for security certificates to verify the trustworthiness of a site. Access services via bookmarked links rather than by clicking email or chat links.
Other security solutions based around virtual private networks (VPNs) are also available which encrypt the users' internet connection when they use cryptocurrency services, particularly on public networks, preventing potential eavesdroppers from listening in. Users should also take care not to post sensitive personal information on social media sites, which attackers can use to structure a targeted spoofed email. Small breaches becoming big losses can be avoided by checking your account activity and responding to irregular transactions right away. Transaction limits and withdrawal delays on exchange accounts can also be used to further protect against unauthorized access, offering users a chance to notice and react to potential breaches.
User-Specific Security Strategies
Small investors that have a moderate amount of cryptocurrency want a middle-of-the-road approach, one that's secure but not overly complicated. Users with a balance of cryptocurrency from $1,000 to $50,000 should use hardware wallets for storage and reputable software wallets for everyday spending. These individuals should focus on learning about the more prevalent scams and phishing tactics, as social engineering often concentrates its efforts on less technical individual investors.
Active traders have heightened security concerns because of frequent interactions with exchanges and the requirement to have available funds for trading opportunities. These users should also be maintaining a distinct line between their trading funds and long-term holdings, with different wallets and perhaps even different exchanges. Multi-signature wallets are able to add that extra layer of security for large trading accounts as they necessitate multiple confirmations to execute large transfers. Active traders in particular need to keep good records of their trades and update their security settings often, since the rapid trading world can result in some oversights.
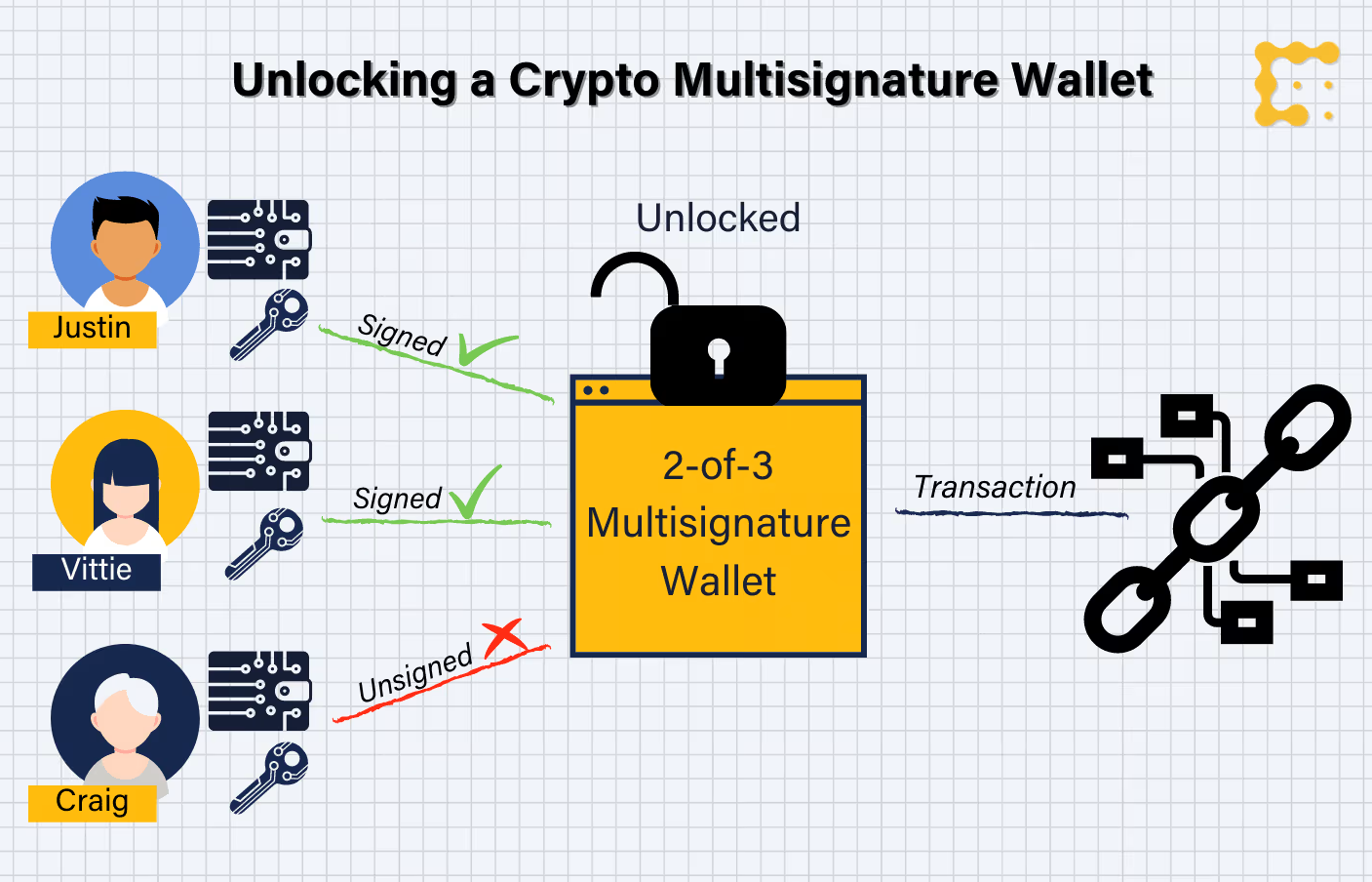
Institutional investors and companies with large cryptocurrency reserves need enterprise-level security solutions that are more than individual users' behavior. For such users, multi-signature wallets become indispensable as multiple authorized parties must acknowledge and verify the transaction, to avoid a single point of failure. Regular security assessments from third-party experts help to find holes before they are breaches, and the best companies will have financial insurance against hacking-related lawsuits. These companies should also establish rigid access controls, employee training programs and incident response methods to effectively deal with security breaches.
Cryptocurrency developers and power users who are working with a cryptocurrency application have more concerns when it comes to security, since it regards their development environment or code. For these users it is recommended to develop on dedicated hardware and network when it comes to cryptocurrencies so their work doesn't affect personal devices or batches of keys. Good secure coding, regular code reviews and responsible handling of private keys and API credentials is the key to avoiding dev-centric security issues. In addition, developers should monitor the newest security bugs in cryptocurrency protocols and employ suitable defenses in their apps.
Why Ongoing Security Training is Necessary
Cryptocurrency security is changing quickly and new threats are constantly appearing as attackers find more advanced attacks. Users need to make the effort for ongoing education about security best practices and remain updated with newly emerging attack vectors and defenses. This education will involve an understanding of the technical aspects of how best to secure your crypto, spotting social engineering attempts and what are the latest security tools and practices. Get involved in crypto communities and follow reputable security researchers. This can give firsthand account on emerging threats and codes to protect your coin better.
Knowing how the technology works allows users to hear about security precautions and infer possible weaknesses. Users do not necessarily have to become technical wizards, but a basic familiarity with the underlying technology and how it functions can go a long way into enhancing overall security. This knowledge allows the users to critically evaluate security claims, so as not to be lured by scams offering either security beyond reason or exorbitant returns.
Ongoing security assessments and updates help maintain protection as adversaries evolve. In addition to the above, users periodically should check in on their security practices - especially tracking password changes and wallet protection and gauging the effectiveness of one's protective measures. This review will need to involve testing new security tools and procedures that offer superior protection to existing measures. Ongoing security assessments locate possible exposures before the bad guys can capitalize on them.
Building a Security-First Mindset
A security-first mindset needs to be established for every interaction with cryptocurrency services, where every single thing is a potential gateway and must be checked. That attitude includes being suspicious of communications, validating that websites and apps are real, and having a proper level of skepticism for offers that simply seem too good to be true. Users should develop clear processes for ascertaining whether cryptocurrency services are legitimate, and never try to circumvent these processes even when on a tight schedule or in response to attractive opportunities.
This security-first culture also involves preparing for potential scenarios before they happen. Wallet users should maintain backups of wallet information in a secure location, and ensure that they have adequate procedures and practice for answering security questions, dealing with hosting related issues, and recovering from certain types of security incidents. Such preparedness can greatly mitigate the effect of breaches and expedite recovery from them.
The establishment of an integrated security plan that addresses all facets of crypto usage will help ensure that no critical security factors are forgotten. This approach should contain detailed, transaction-specific processes for how different transactions will be addressed, procedures for determining new services and applications that are used in business implementations and process flows, and instructions on how security issues will be handled. Regular analysis and replanning of the security plan will keep it valid as long as user's crypto usage changes.
More Advanced Security Concerns and Some New Threats
The world of cryptocurrency has no choice other than to adapt and with continued evolution in the system comes new security challenges, which need a higher level of protection. Quantum computing is also a prospective threat to existing cryptography algorithms, and it is important for end users to keep track of advancements in post-quantum cryptography. Quantum computers that can defeat today’s public-key encryption have not been built, but the cryptocurrency industry has already begun working on quantum-resistant algorithms in order to be ready for when it happens.
Social engineering attacks are also becoming more advanced, with attackers leveraging deepfake technology and AI-generated content to develop lifelike impersonations of familiar individuals or brands. Individuals will still need to stay on top of confirming who is seeking sensitive details or currency exchanges, even if they think the query is from someone they know. Multi-touch validation, including verifying requests through a different communication channel, can help guard against these advanced social engineering attacks.
The advent of decentralized finance (DeFi) applications has added a new security concern: DeFi sites frequently require action from users who interact with smart contracts, which may be flawed. With any DeFi platform, users should do their own research before depositing money and look for security audits, community reviews, and the platform’s history. The risks surrounding yield farming/liquidity provision, and DeFi activity more broadly are critical considerations when choosing to participate in these protocols.
There has been an accelerating need for mobile security as a larger number of users connect to crypto services via smartphones and tablets. Malware is a problem especially for unofficial apps on mobile devices. Consumers should only download cryptocurrency apps from official app stores, and verify the developer of an app before downloading it. Frequent security updates for mobile apps and systems are key in order to keep devices secure.
Transaction Security
For the sector of cryptocurrency transactions, we offer users solutions that are efficient in both security and pricing when navigating platforms like TRON. This Energy rental system allows users to save as much as five times in transaction costs (in TRX) without staking or freezing assets, maintaining full permissionless control of their own holdings.
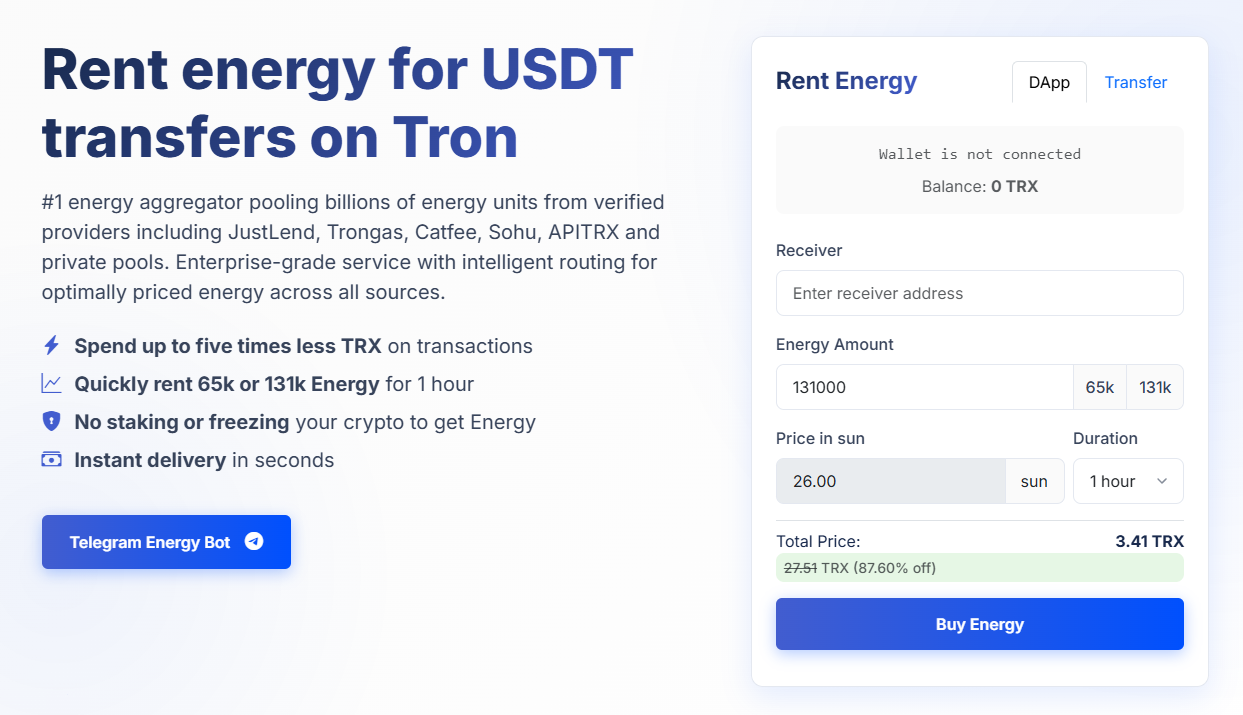
Thanks to Netts' TRON Energy rental service, our users receive huge discounts in combination with enterprise-level security. The platform's non-custody nature allows users to still have full control over their private keys during the Energy renting process, removing most of the security vulnerabilities that pose critical issues while achieving transaction optimization.