Purely Technical Problems of Cryptocurrencies
Bandwidth, mining hardware, smart-contract risk, AI overhead, and mobile limits — blockchains still hit hard engineering walls.
The decentralized nature of cryptocurrencies has disruptive potential for digital finance but introduces significant technical challenges regarding scalability, efficiency and global availability. Although the principle of blockchain technology sounds beautiful, the design needs to solve many engineering technical problems in practice from infrastructure, hardware, energy consumption and software. These are purely technical barriers which demand advanced solutions and constant innovation to maintain the sustainable growth of coin ecosystems.
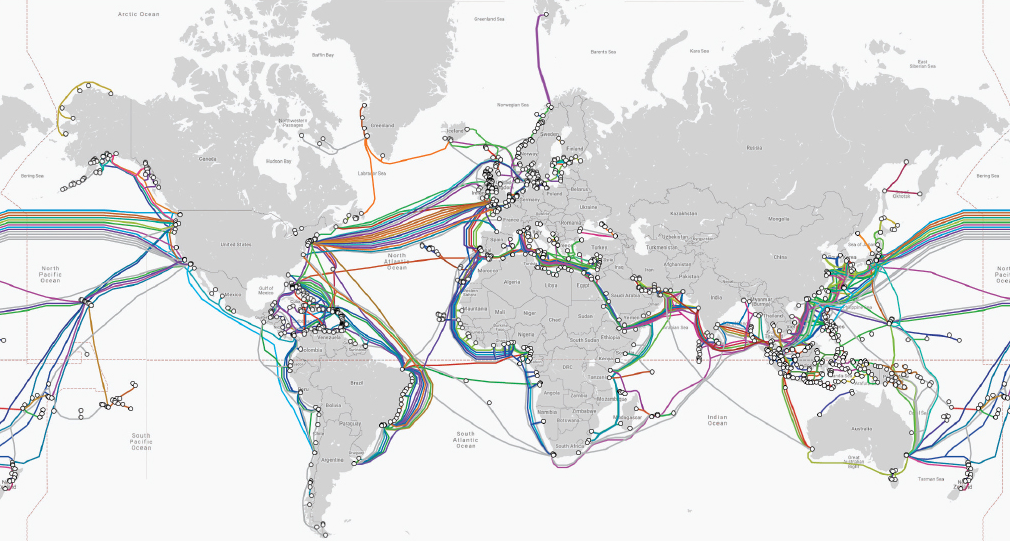
Limitations of Bandwidth between Regions of the World
All cryptocurrency networks need is a blanket of internet coverage, but the reality is that internet infrastructure around the world is inconsistent not just across continents, but also among rich and poor. Roughly 2.9 billion people around the world are deprived of internet, most of them in sub-Saharan Africa, South Asia and rural areas of developing countries. This digital gap presents a high hurdle for the adoption of cryptocurrencies in those areas where decentralized finance systems would be most valuable. The overcentralization of mining and validation with the concentration of mining activity in well-connected locations raises a question about blockchain systems' distributed essence (not only technically but also geographically): do we see geographic centralization that runs counter to the foundational principle of decentralization?
Bandwidth limitations also constitute another problem of the utmost importance for users and network providers. Nowadays, cryptocurrency networks produce a lot of data traffic, with Bitcoin blockchain size being over 500 gigabytes and Ethereum closing in on 1 terabyte. These ledgers require a lot of bandwidth to stay up-to-date, making an adversarial strategy especially severe in areas where internet is sparse and speeds are orders slower than MB/s. Transaction propagation delays grow exponentially with bandwidth constraints and slow down the confirmation process and network capacity. With the rise of layer-2 solutions and sidechains, bandwidth demands have multiplied, adding pressure on infrastructure.
Network latency is an especially difficult problem for cryptocurrency operations. It takes different geographically dispersed networks varied lengths of time to receive transaction information. High latency connections can lead to transaction ordering discrepancies, facilitating front running and abuse of the market. Low-latency trading systems have created a virtual arms race for network proximity to popular exchanges, further centralizing some aspects of cryptocurrency infrastructure around financial centers.
Undersea cable reliance introduces systemic vulnerabilities to cryptocurrency networks that are more than just the usual suspects when it comes to connectivity problems. 99% of international data is transmitted through some 400 sub-oceanic fiber cables that stretch 1.3 million kilometers between continents across sea beds. The cables are at risk of physical damage by natural disasters (earthquakes, tsunamis), ship anchors from commercial vessels that range across the oceans in search of the shortest path between ports, and fishing gear that accidentally snares a cable line or deliberate sabotaging by state or non-state actors. One break in a cable can cut off entire regions from cryptocurrency networks, resulting in transaction delays, potential forks and broken consensus protocols. And the density of undersea cable landing points introduces more weak links: Much of the world's intercontinental traffic is routed through a few dozen coastal hubs, and severing just a handful could temporarily disrupt all sorts of exchanges.
Hardware Requirements and Power Consumption Overhead
Cryptocurrency mining requires specialty hardware designed to be optimized for cryptographic hash functions that need to do billions of computations per second on a very low energy budget. ASICs are the result of sophisticated engineering and are the most advanced form of hardware mining available today, recently hitting in excess of 200 terahashes per second at consumption levels over 3,000 watts each. These devices are made with leading-edge semiconductor manufacturing processes that go down to a 7nm or smaller process node, and they have supply chains running across multiple continents. Typical development time for new ASIC generations is 12 to 18 months, with high capital expenditures that can exceed $100 million for the most advanced products.
The power consumption of cryptocurrency networks has become significant and is straining conventional electricity grid infrastructure. Bitcoin's network uses roughly 150 terawatt-hours in a year, about as much as Argentina or the Netherlands. This enormous energy requirement puts new pressure on power generation and distribution, and has even caused grid instability in some areas — again because of the extreme concentration of power consumption by miners. Ethereum is already on the path to 99.95% reduction in energy consumption through proof of stake, but other proof-of-work networks consume significant amounts of power that have been a stress test to local power infrastructure.
The environmental effect of cryptocurrency mining is not just in utilizing electricity, but also the need for cooling, manufacturers' emissions and e-waste. ASIC chips consume large amounts of rare earth elements and the process of their production contributes to a substantial amount of carbon emissions. With mining hardware becoming obsolete so quickly, e-waste is an ongoing concern and potential environmental disaster in regions with little or no recycling capabilities. Mining equipment distribution is burdened by a complicated logistical situation that takes its roots in different countries and legal complexities, with certain key production facilities being located in particular territories leading to supply chain bottlenecks that can be even worsened due to geopolitical disturbances or natural catastrophes.
Challenges in Programming and Smart Contract Security
The design of cryptocurrency protocols entails solving complex systems problems across multiple disciplines involving cryptography, distributed consensus, incentive mechanisms and consensus mechanism engineering. The complexity of these systems has risen by orders of magnitude as blockchain networks have matured from elementary transaction ledgers into comprehensive platforms for complex financial products and decentralized applications. Smart contracts bring even more power and complexity into the mix due to their unchanging character and immediate financial consequences, which mean that one mistake in writing code can lead to dollar amounts found only in computer screen legends going up in smoke.

Though the Solidity language is in common use for smart contracts based on Ethereum, it harbors many pitfalls that tend to result in serious vulnerabilities. Typical problems are integer overflow and underflow conditions, reentrancy patterns by exploiting recursion in function calls, undue authorities for users to perform unauthorized operations and front-running vulnerabilities for market manipulation. In addition, the limited instruction set and stack-based architecture of the EVM present further complications to developers used to more common programming styles. Because debugging or testing toolset is not well developed, even subtle bugs are hard to find when the new instruction is deployed.
Formal methodologies have become necessary means of guaranteeing the security of smart contracts, though these often need specialized knowledge and high computation costs to be useful. These mathematical techniques can be used to specify and to verify that contract logic is correct with the aid of theorem provers and model checkers, but it can be an uphill battle to perform a complete verification in complex systems like DeFi where several contracts interact. The verification of such propositions usually take months of work by teams of specialised mathematicians and computer scientists, something that is unfortunately not feasible for most of the smaller projects. Automated testing frameworks (e.g., KLEE, CREST), and static analysis tools provide partial solutions but cannot replace human intuition who is able to identify subtle vulnerabilities that automated tool may miss.
Cross-compatibility is a permanent test for cryptocurrency systems designed to work flawlessly across various operating systems and hardware platforms. There are different security models, memory handling routines, crypto libraries and network stacks in the operating systems. Making sure that the code works consistently on all supported platforms: Windows, macOS, Linux, iOS and Android is a long process that requires thorough testing and adaptations specific for each platform which can make development take longer and become more complex. The use of hardware security modules (HSM) and trusted execution environments (TEE) further complicates cryptocurrency development by calling for bespoke programming interfaces and platform-dependent implementations.
Artificial Intelligence Integration and Computation Challenges
Artificial intelligence in cryptocurrencies offers extraordinary possibilities and challenges to the way distributed networks are initially built. AI is able to improve security by means of advanced systems that can detect anomalies in transaction patterns, investment strategies algorithms based on machine learning and that adapt themselves to market conditions, fraud prevention with behavioral analysis and risk assessment algorithms. But AI also requires significant computational capacity that could overload current network infrastructure and create fresh opportunities for adversaries to launch attacks.
In general, machine-learning algorithms often run on custom-designed hardware accelerators (e.g., graphical processing units [GPUs], tensor processing units [TPUs], field-programmable gate arrays [FPGAs]), which also contributes to the total energy consumption for cryptocurrency mining as well. The computational costs of training and inference can be immense – large language models can require hundreds of gigabytes of memory and need to process ROPs or teraflops. The introduction of these systems on blockchain networks leads to new consensus problems since AIs calculations cannot be deterministic, and/or known by every member of the network.

Guaranteeing algorithmic transparency and fairness in AI based cryptocurrency systems poses unprecedented challenges since it contradicts with the decentralization offered by the blockchain based networks. Central oversight of the kind needed to update and maintain AI models goes against the decentralized governance that characterizes cryptocurrency systems. Federated learning methods offer possible solutions which allow model training to be distributed and also preserve network decentralization, but the construction of such systems involves complex coordination mechanisms and robust communication protocols capable of tolerating network fragmentation and Byzantine failures.
The cost of AI incorporation into their network could mean that having to generate any level of outputs worth the money it will take up front just won't work. AI processing in real-time for security monitoring or trading optimization must run with the most low-latency performance possible, a requirement which is likely at cross purposes with blockchain’s consensus mechanisms crafted more for security and decentralization than speed. The addition of AI also creates new security vulnerabilities and attack surfaces that need be taken into account, such as adversarial machine learning attacks which can tamper with AI models through well-crafted inputs, breaking security systems or allowing the manipulation of markets.
Mobile Optimization and Cross-Platform Compatibility
Smartphone hardware has some limitations such as low processing power compared to PCs, tiny memory size restricting the complexity of cryptographic operations, and limited battery lifetime necessitating energy efficient management. Running a full node on mobile is currently not possible from the storage aspect, which can easily exceed 100 GB or the bandwidth perspective (will easily consume data caps), requiring Light clients that piggy back off someone else's infrastructure and can introduce centralization issues.
SoC/gear heterogeneity makes optimizations hard and calls for intelligent adaptive algorithms. A wide variety of screen sizes from small screens to large portable devices to even larger desktop monitors, differing screen resolutions ranging from low (QVGA) to high definition (HDTV and so on) can also be accommodated by the System and the User Interface should consider these at all times. Performance optimisation has to take into consideration different processor architectures such as ARM, x86 and custom chipsets, various memory capacities between 2GB to 16GB and battery capacity which influence how long the device can run in intense cryptographic computations.
The threat model of mobile devices, makes security for mobile crypto-currency applications more challenging. Mobile operating systems introduce different security paradigms iOS is sandboxed, preventing applications from accessing system resources in Android the configurations can include deeper integration into the system posing a higher attack surface. To store secure keys, one needs to use per-platform secure enclaves and trusted execution zones, while cross finger print readers, face detection systems, or voice recognition software support is necessary for biometric authentication.
The threat landscape across mobile is rife with advanced attack vectors, like malware that can capture keystrokes or screen content; network attacks which take advantage of open Wi-Fi networks or other kinds of public vulnerabilities and physical compromises to further frighten and unlock device. The use of secure communication protocols must also integrate the support for certificate pinning, perfect forward secrecy and protection against man-in-the-middle. Cross-platform development frameworks have been developed to try and overcome these difficulties, where they offer the same set of APIs to develop applications on different mobile platforms; however, this often introduces performance overhead and restrictions that ultimately may lead to security risks or poor user experience.
Energy Management Solutions and Automation
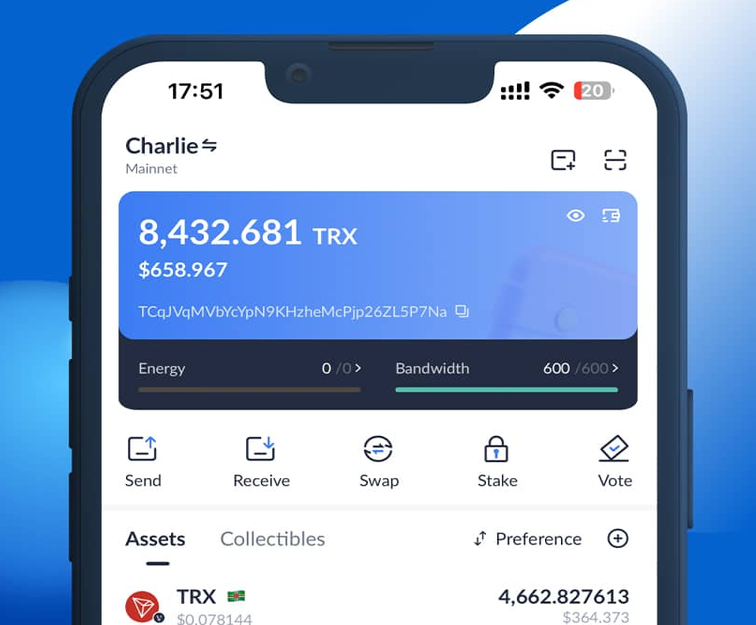
To cope with the intricate energy demands presented by cryptocurrency networks, an advanced automation solution is needed that can allocate resources optimally while still being cost efficient. Startups such as Netts have come up with creative solutions to the problem of Energy delegating, providing streamlined systems for an unlimited supply of Energy for TRON transactions — through use of understandable API.
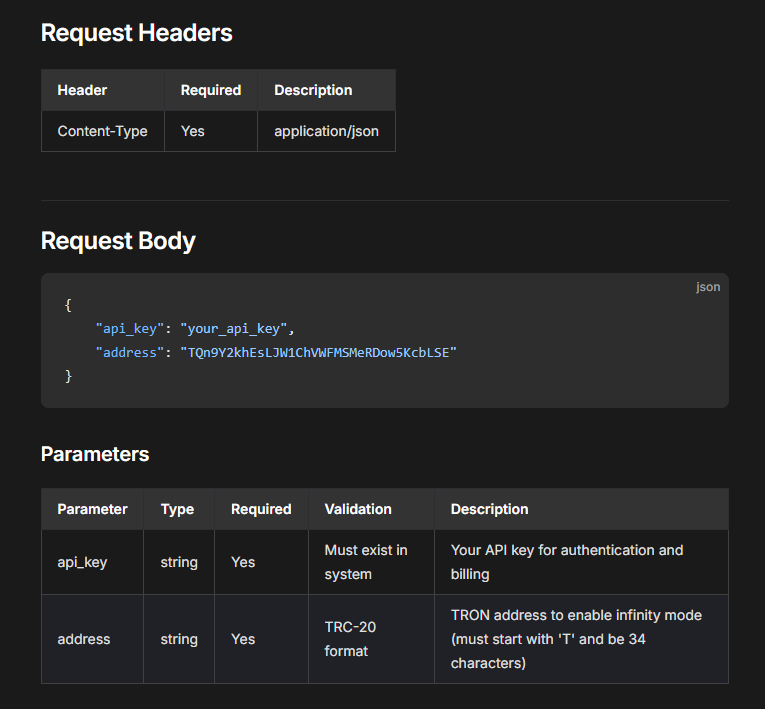
Through smart automated Energy rentals, users can secure great prices for TRON Energy with none of the manual management burden — a typical example of how technical advancement in automation assists the operational challenges facing cryptocurrency infrastructure.