Hacking in Crypto - Cybersecurity of Blockchain
Bybit-scale hacks vs. blockchain cryptography: cold storage, seed phrases, 2FA, approvals, and staying safe on TRON — without trusting exchanges alone.
The month of February 2025 will be unforgettable for the crypto community as that was when the unthinkable took place. It began as a typical Tuesday, with markets ticking in their normal patterns and traders watching screens, parsing charts and sipping coffee. Bybit, a giant in the exchange business, with millions of users worldwide, was supposed to be too large to fail. Its security procedures were legendary, its reputation sterling and its user base confident that their digital assets were safer there than in a vault at Fort Knox.
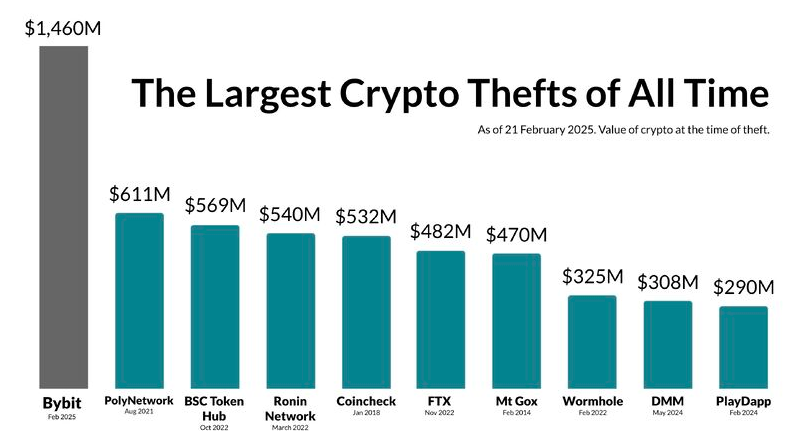
Then the notifications began popping up — mystified tweets at first and then too-excited Reddit threads. Withdrawals were paused. Balances were showing errors. For the first hour, the silence from official channels was deafening: a void of information that sucked hope away from millions of chests. And then it finally happened, the announcement that punctured the bubble of invincibility: there had been a catastrophic security breach which leveraged a vulnerability in its multi-signature wallet implementation. Some 1.5 billion dollars of Ethereum had been drained away in minutes, and disappeared into the digital ether of the blockchain.
And the human cost of an event like this is often overlooked amid the shocking tallies of headlines. It’s easy to imagine “investors” as anonymous entities, but the truth is much closer to home. There was Sarah, the graphic designer who had been stashing away every penny she could toward getting a down payment for her first home, and trusted their platform with her life savings because she believed the “bank-grade security” marketing.
There was Michael, a retiree who had set aside some small percentage of his pension for crypto, in the hopes it might represent a small legacy for his grandchildren, and now sat at a screen that told him that piece of money no longer existed. These are people who woke up one morning thinking the worst thing they had to worry about was their stocks taking a dip in the market, not that all their money just disappeared because some system scaled too fast and failed over which they had no control.
They also figured, quite reasonably, that the kind of company with its enormous resources and visibility would never fall prey to a hack of this scale. It was a rude awakening to the fact that in the digital wild west, big does not necessarily mean invincible. The psychic blow was sudden and devastating; the breach didn’t just take money, it took peace of mind.
From Titans of Industry to Bedroom Coding
That threat isn’t exclusive to the world of cryptocurrencies, but in the crypto wilderness it’s generally harder to erase or overwrite mistakes. There are too many stars throughout history of some of the most recognizable companies on earth, entities with nigh-limitless budgets for cybersecurity, succumbing to hackers.
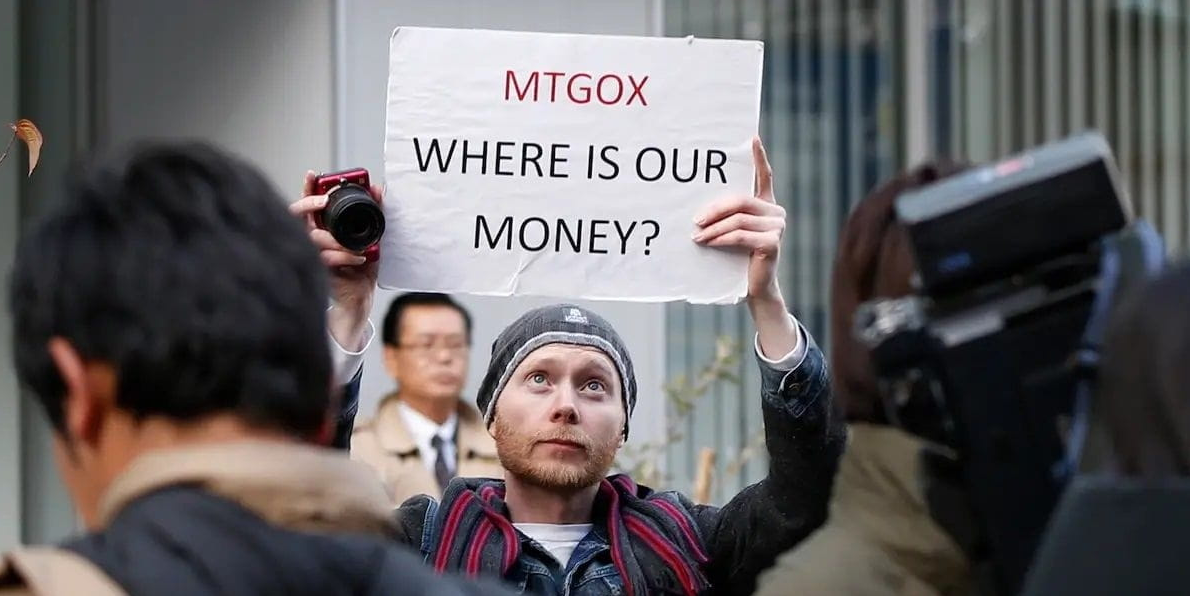
Think about the huge data breaches on Yahoo where billions of accounts were compromised, or the Equifax fiasco where sensitive financial information on almost half of all Americans was exposed. Even a tech behemoth like Sony was brought to its knees, with the PlayStation Network breach revealing millions of credit cards. These weren’t fly-by-night operations; they were institutions of the modern economy with armies of security engineers. If they could be penetrated, the argument goes, what chance does a digital currency platform have? This backdrop is important, as it sets the tone for the skepticism of mainstream investors toward the crypto space. They read the news about Bybit, or about the historic Mt. Gox crash and they piece together a history of instability that confirms their worst fears.
In cryptocurrency, the problem is frequently amplified due to its innovative nature. Unlike the lumbering old banking system that is heavily regulated and moves at a snail’s pace, the crypto industry lives life in the fast lane. Plenty of projects with valuations in the millions or even billions began as a scribble on a napkin and were hacked into existence by an undersize team — sometimes composed of just one developer — hunched over a laptop in a shared workspace or basement.
This “move fast and break things” culture is the bedrock of innovation, but it’s also a hotbed for security blind spots. A bank? It could spend years experimenting with a new transaction layer; a crypto startup might deploy a new smart contract over the weekend to capitalize on whatever meme is currently trending.
From the viewpoint of an institutional investor, this doesn’t resemble a closely plotted financial revolution so much as it does one big, blind string of dynamite. It’s also a perception that the ecosystem is built on brilliant but foolhardy amateurs playing with fire, in which one missing line of code can drain a protocol entirely of its liquidity. This “wild west” perception is a major impediment to gaining mass adoption, as the average person does not want to fear that their money may vanish simply because some developer failed to audit one particular function.
The Fortress in Your Pocket
But there is a twist in this story, one rarely told. And for all its power and probability compared to the madness of crypto's charge into our lives, it is an upturn in the plot. The technology that permits these hacks also provides us with the means for greater personal security, if we use it right.
The “good” news is that the blockchain is probably one of the most secure systems ever created. If you peel away the centralized exchanges and hastily written smart contracts, the underlying cryptography of networks like Bitcoin, Ethereum and TRON cannot be cracked by even today’s best math. So long as a user is cautious and understands how custody works, their funds in some ways could be safer than at a traditional bank. In a bank, your money is a liability on the bank’s ledger; in a non-custodial crypto wallet, your money is codified as data — information stored on an immutable ledger that only you have access to. There’s not a bank manager who can freeze your account, no bank holiday that locks you out and (if secured properly) no hacker who can brute-force a stolen private key.
This move necessitates a shift in mindset — from depending on someone else for our protection to self-assuming complete responsibility over our own cyber hygiene. It’s a scary leap, but it is the fundamental promise of cryptocurrency: real ownership. Almost invariably, the horror stories of hacks feature some form of centralization or user error — a bad password, a compromised seed phrase or mindless reliance on a third-party custodian. If a man blocks these weak points, he is his own fortress. The walls around that are more secure than any bank vault door.
The challenge — and the solution — is purely educational and behavioral. Through a combination of “zero trust” and knowledge of the vectors, one can somehow work in this crazy crypto world with a level of security that was previously only available to governments and billionaires. It flips the weakness of startup laptops on its head: You don’t need to have a billion-dollar security budget, you just need a series of strict, unbreakable habits.
Becoming an Expert at Crypto Security
Safely maneuvering this terrain requires that one take a layered approach to security, dealing with their digital property in the same paranoid and respectful fashion they would if they had a stack of gold bars sitting in their front room. The first and most important rule is to keep your money separated. Never leave large amounts of cryptocurrency on an exchange.
As was shown with the Bybit event, “not your keys, not your crypto” is more than a catchy slogan — it’s a survival rule. Exchanges are prime targets for hackers; by moving your money to an offline cold storage hardware wallet, you take it out of the game. With a hardware wallet, your private keys are never exposed to the internet so even if you have the most advanced of malware on your computer or phone, an attacker is unable to sign a transaction without having physical access to your hardware device. Air-gapped security is the gold standard in crypto and your first purchase upon entering the space.
Aside from the hardware itself, safeguarding your recovery phrase is vital. This chain of 12 or 24 words is the master key to your financial kingdom. One big mistake: Saving the phrase should not be digital -- do not take a screen shot, file it as text or even ask someone to email it to you. This is like locking your front door but leaving the key taped to the outside of it.

If your cloud storage or email account is hacked, then your wallet’s out the door. The irrefutable truth is that a seed phrase can only be stored securely physically, written on paper or better yet stamped into a metal plate that can survive burning and flooding. This last physical backup probably belongs in some safe (also possibly in pieces and spread into another part of the country). It might sound extreme, but when you are your own bank, you must think like a vault manager.
1. Don’t get phished or socially engineered. Most people get their crypto stolen not by a computer exploit, but through a basic confidence scam. Hackers will make counterfeit versions of real websites, send emails impersonating staff or DM you on social platforms offering “help” or “airdrops.” Always use the official sites of the services you employ as a bookmark, and never click on them from search-engine ads or email links. Always remember: Any support professionals helping you is never going to ask for your seed phrase or private keys. If they demand it, then they’re trying to rob you.
2. Smart contract hygiene. When using DeFi protocols, there is often a step where you have to “approve” a contract to spend your tokens. An easy mistake is to give "unlimited" permissions to the above contracts. Then, if someone ever uses or finds that contract — whether two weeks or six months down the line — the attacker can suck out every approved token you let them. Approve only what you need to and check in periodically to revoke allowances for old dapps you're not using.
3. Two-Factor Authentication (2FA). For anything that requires a login, 2FA is the least you can do. But not all 2FA is produced equal. SMS-based 2FA is susceptible to “SIM swapping,” when a hacker tricks your mobile carrier into transferring your phone number to their SIM card. Once they have your number, they can snag your 2FA codes. Always opt for an authenticator app (like Google Authenticator or Authy) or, better yet a hardware security key like a YubiKey. This means that you need to have the device in hand in order to access your account.
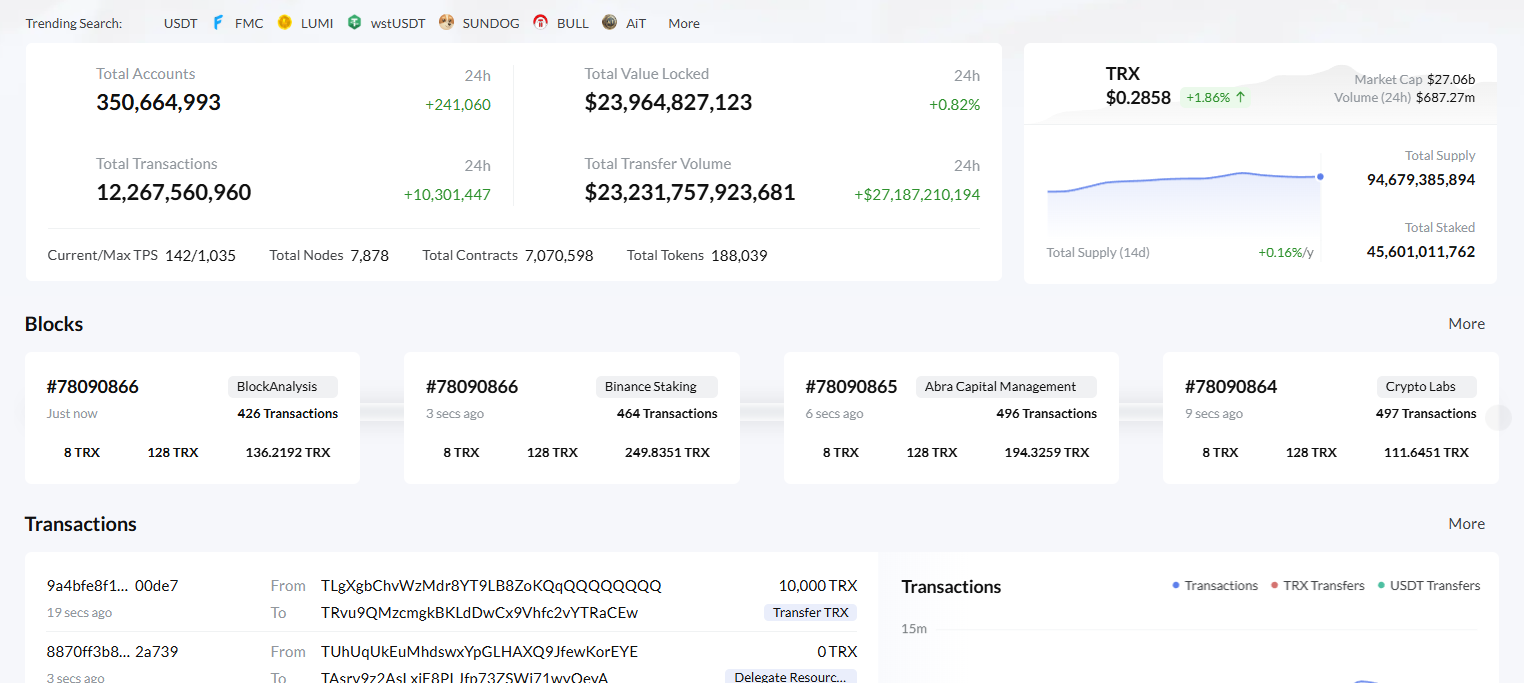
4. TRON Network and resource management. Security on any blockchain such as TRON also means learning how the network operates. The security of TRON is very good, it uses just a Delegated Proof of Stake system to do so, but users usually incur unnecessary risks when playing around with transaction fees. On TRON, transactions require “Energy” and “Bandwidth”. If the user does not have sufficient frozen or rented of these resources, they burn TRX from their wallet to cover the transaction. It's one of those things that can be unexpectedly costly for users.
Navigating the TRON Ecosystem
The TRON Network – A powerhouse for USDT transaction security in terms of speed and cost, but it comes with its own unique set of security challenges. The resource model is one of the special targets of TRON. Unlike Ethereum, where you do just pay a gas fee, on TRON you are able to stake TRX in order to produce Bandwidth and Energy.
Bandwidth is consumed for average transactions, and Energy is consumed for invoking smart contract functions (e.g., sending USDT). In this case, though, the network isn't really to blame; it's the system of third-party sites that claim they're offering you Energy for cheap. Those who want to purchase TRON Energy safely should keep their eyes peeled. Many scam sites which purport to rent you energy (Energy) for prices much less than what we do, but instead require that you sign a malicious permission granting them access to your wallet.
When entering the world of TRON, it’s important to stay safe so make sure to double check that the platform you’re utilizing to rent Energy is legit. There ARE legitimate markets to safely lend assets if you trust that you won't lose your coins. When you safely purchase TRON Energy from a reliable provider, you are in fact paying a fee to rent the resources you need for your transaction, preventing yourself having to burn such a massive amount of TRX.
As long as the transaction you're signing is a "delegate" or "transfer" transaction, rather than "approve" or "update permission", this mechanism should be perfectly safe. You read what your wallet asks you to sign. If you are only renting Energy, you should never have to give your private key or allow spending on your tokens.
One more thing that we need to look into is the TRON security and multi-signature permissions. TRON supports arbitrary account relationships where multiple keys are required to sign a transaction. That’s great for businesses but a trap for individual users if they unwittingly alter the permission structure of their accounts.
Sometimes hackers dupe users into “updating” their account permissions, which then locks the user out of their own wallet. You should always be VERY suspicious of any website that asks you to change "Active" or "Owner" permissions. And by staying with common transactions and reliable platforms for resources management, you can take all the advantage of TRON fast speed without getting caught up in these fancy traps.
In the speedy universe of blockchain, only knowledge is armor. Whether you are holding onto Bitcoin long-term or transacting up and down USDT on TRON every day, the basics still apply: Trust no one; verify everything; keep your keys offline. You can safely traverse the dark labyrinth of hackers and exploits — but only if you’ve taken the time to learn the map. Through securing your digital perimeter and gaining knowledge of the way networks operate, you go from potential victim to an independent financial entity in control of your destiny.
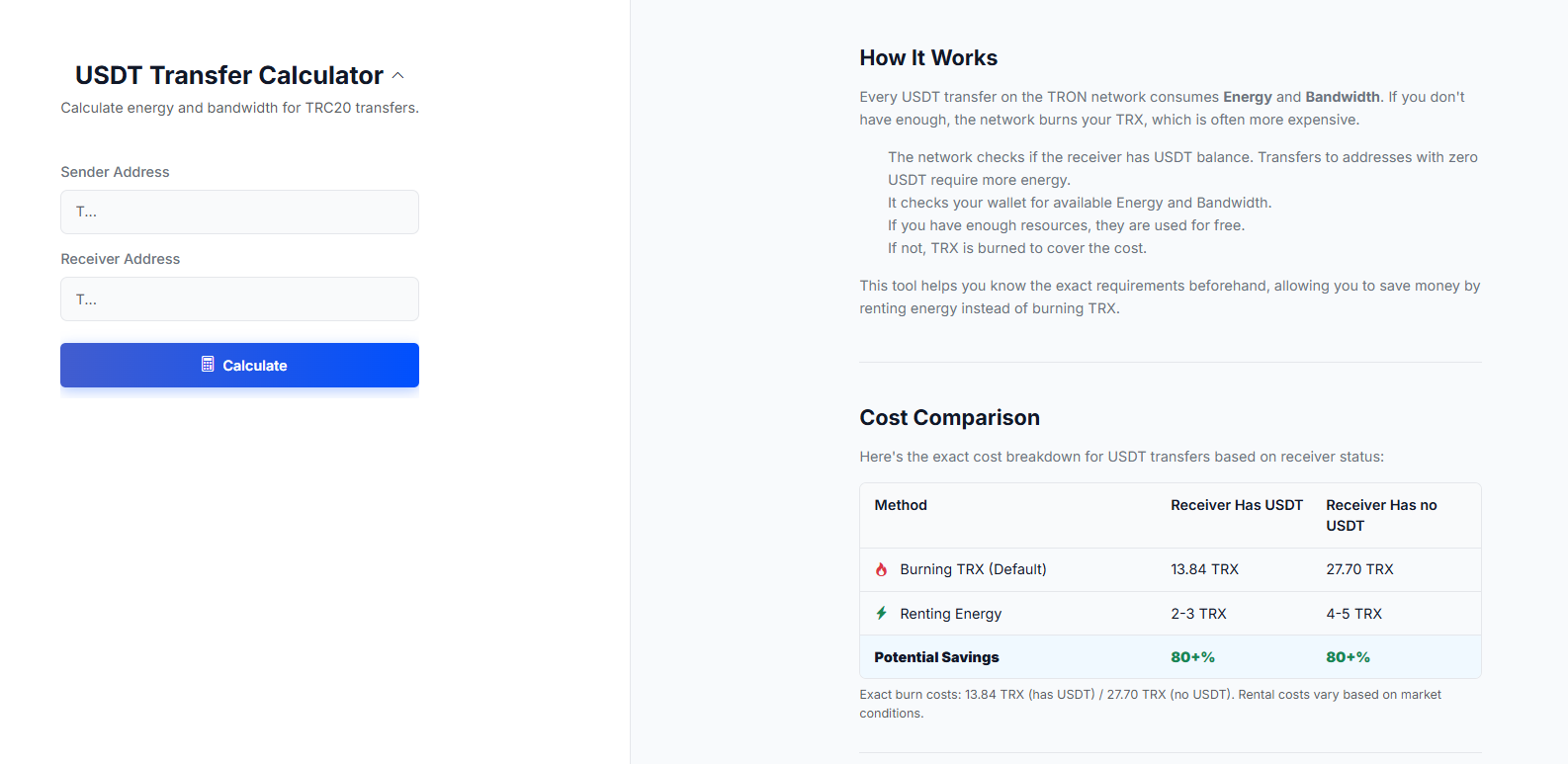
For frequent users, it is essential to operate securely and efficiently, this includes the management of transaction costs when using the TRON network. That's why tools like Netts include a USDT Transfer Calculator to enable users to calculate the exact Energy and Bandwidth required for their specific transfers. By ensuring the receiver’s balance status (which will cost them more if sending an empty wallet) and by measuring the exactly required resources, traders can prevent unexpected TRX Burns and make their transfers secure as well as inexpensive.